OpenClaw 2026.3.12 & 3.13 Security Upgrades
AI SAFE² SECURITY ANALYSIS
OpenClaw 2026.3.12 & 3.13 Security Upgrades
From Ecosystem Hardening to Semantic Gap Triage —> Analyzed Against AI SAFE²
Series: OpenClaw Security Upgrades — Ongoing Analysis (Part 8)
Releases Covered: 2026.3.12, 2026.3.13-beta, 2026.3.13
Phase 8: Closing the Semantic Gap Between What You See and What Executes
OpenClaw Security Upgrades releases 3.12 and 3.13 are, by volume of coordinated security advisories, the most intensive vulnerability triage in the project’s history. Over a dozen GHSA closures in two releases. But the technical depth is more significant than the count. These patches address a class of threat that previous phases could not: the semantic gap—the distance between what a human reads in an approval prompt, what the parser evaluates against the allowlist, and what the operating system actually executes.
Invisible Unicode characters that render zero-width in approval prompts but execute as real commands. Compatibility code points that bypass obfuscation heuristics after normalization. Wrapper scripts pnpm, npm exec, Perl -M, PowerShell -EncodedCommand that smuggle blocked payloads through approved execution shells. Cross-site WebSocket hijacking that grants untrusted browser origins operator.admin access regardless of proxy headers. Plugin auto-loading from cloned repositories without explicit trust decisions.
Where the 3.1–3.7 releases secured the trust boundary between the platform and its extensions, the 3.12–3.13 releases confront a more fundamental truth: the security controls built in Phases 4 through 7 are only as reliable as the parser’s ability to interpret input identically to the operating system. When those interpretations diverge—through Unicode tricks, wrapper smuggling, or scope injection—the controls become decorative.
“What the human sees, what the parser reads, and what the OS executes are three different things. Security lives in the gaps between them.”
The development team’s response is thorough and impressive. It is also, by definition, a game of enumeration: each GHSA addresses a specific parsing discrepancy that was discovered, reported, and fixed. The adversary had the initiative. A new Unicode encoding, a new wrapper script, a new scope-injection technique will require a new patch. This is the structural constraint of parser-level defense.
This analysis evaluates the specific vulnerability closures across both releases, extends the eight-phase maturity model, and demonstrates why the AI SAFE² Framework remains the governance layer that parser-level triage cannot replace.
Security Evaluation: What 3.12 and 3.13 Actually Fix
These releases deploy a concentrated burst of coordinated vulnerability patches across four attack surfaces. Each GHSA closure addresses a specific technique for exploiting the semantic gap between display, parsing, and execution.
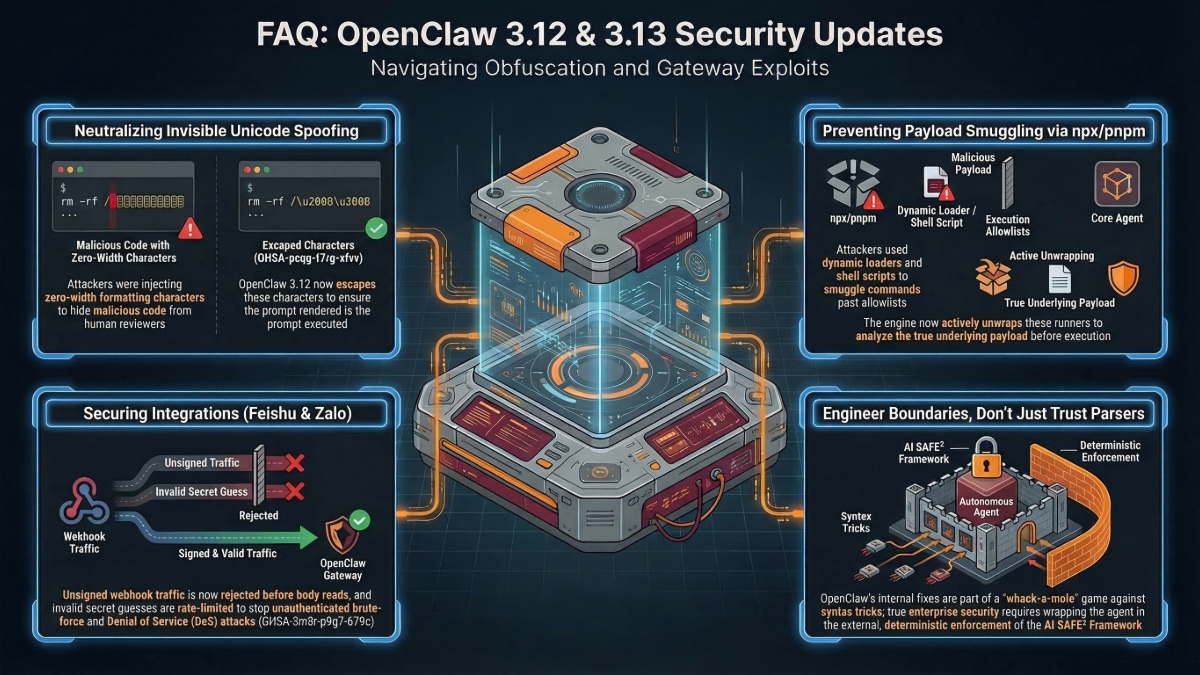
A. Command Evasion and Obfuscation Defenses
The execution pipeline receives the deepest parsing-level hardening in the project’s history, addressing three distinct evasion classes.
- Invisible Character Spoofing (GHSA-pcqg-f7rg-xfvv): Invisible Unicode formatting characters—zero-width joiners, zero-width spaces, right-to-left marks—are now escaped in approval prompts so they render visibly. Previously, an attacker could insert invisible characters into a command that appeared benign in the approval UI but executed a completely different payload. The human approver saw one command; the OS executed another.
- Unicode Normalization (GHSA-9r3v-37xh-2cf6): Invisible formatting code points are stripped and compatibility Unicode is normalized before obfuscation checks run. Without this fix, an attacker could use Unicode compatibility decomposition to construct strings that looked identical to allowed commands but contained different underlying code points that bypassed the obfuscation heuristics.
- Wrapper Smuggling (GHSA-57jw-9722-6rf2, GHSA-jvqh-rfmh-jh27, GHSA-x7pp-23xv-mmr4): The execution engine now fails closed for ambiguous inline loader and shell-payload script execution. Complex wrapper forms—pnpm, npm exec, Perl -M, PowerShell -EncodedCommand—are unwrapped and their inner payloads evaluated against the approval bindings. Previously, an attacker could execute a blocked command by wrapping it inside an approved package manager or script interpreter that the allowlist treated as a single permitted binary.
B. Gateway, WebSocket, and Network Lockdown
- WebSocket Hijacking — Critical Fix (GHSA-5wcw-8jjv-m286): Release 3.13 enforces browser origin validation for all browser-originated WebSocket connections regardless of proxy headers. This closes a cross-site WebSocket hijacking path where untrusted browser origins could obtain operator.admin access by connecting through a proxy that stripped or spoofed the Origin header. This is a direct evolution of the ClawJacked vulnerability class first addressed in 2.25.
- Pre-auth DoS Defense (GHSA-jv4g-m82p-2j93, GHSA-xwx2-ppv2-wx98): Unauthenticated handshake retention is shortened and oversized pre-auth WebSocket frames are rejected before application-layer parsing. An attacker who opens a WebSocket connection and sends oversized frames can no longer exhaust parser resources before the connection is authenticated.
- Token and Scope Bleed (GHSA-2pwv-x786-56f8, GHSA-rqpp-rjj8-7wv8): Issued device-token scopes are now capped to the paired device’s approved baseline. Unbound client-declared scopes on shared-token WebSocket connections are cleared. Previously, a device-less operator connecting via a shared token could self-declare elevated scopes—effectively granting themselves admin access by claiming it in the connection handshake.
- Docker Credential Leak: Gateway tokens are prevented from leaking into the Docker build context, closing a vector where CI/CD build artifacts could contain production credentials.
C. Plugin and Workspace Containment
- Plugin Auto-Load Block (GHSA-99qw-6mr3-36qr): Implicit workspace plugin auto-loading is disabled. Previously, cloning a repository that contained a workspace plugin directory could execute plugin code without any explicit trust decision. An attacker who crafted a repository with a malicious workspace plugin could compromise any developer who cloned it.
- Browser Control Surface (GHSA-vmhq-cqm9-6p7q): Persistent browser profile create and delete routes are blocked from write-scoped requests. Only admin-scoped requests can create or destroy persistent browser profiles, preventing unauthorized persistence of profile changes that could alter the browser’s security configuration.
- Session State Visibility (GHSA-wcxr-59v9-rxr8): Sandbox session-tree visibility and shared agent-to-agent access guards are enforced. Sandboxed sub-agents can no longer inspect parent session metadata, closing an information leakage path where a compromised sub-agent could read the parent agent’s session context including credentials and conversation history.
D. Webhook Authenticity and Spoofing
- Feishu/Lark (GHSA-g353-mgv3-8pcj, GHSA-m69h-jm2f-2pv8): Webhook mode now requires encryptKey alongside verificationToken. Without both, forged events are rejected. Typing lookup is preserved to prevent group authorization bypass via p2p reactions—an attacker could previously bypass group-level authorization by triggering the agent through person-to-person reactions rather than group messages.
- LINE and Zalo (GHSA-mhxh-9pjm-w7q5, GHSA-5m9r-p9g7-679c): Signatures are now required for empty-event POST probes—a technique where attackers send empty webhook bodies to test whether an endpoint is active without triggering content validation. Rate limiting is applied to invalid secret guesses, preventing brute-force authentication attacks against webhook signing secrets.
Trajectory Analysis: Eight Phases of OpenClaw Security Maturity
Releases 3.12 and 3.13 establish the eighth phase: Semantic Gap Triage. The focus has shifted from hardening boundaries to closing the parsing discrepancies that undermine them.
Phase | Releases | Focus | Philosophy |
1 | 2026.1.29–2.1 | Removed “None” auth; TLS 1.3; warned on exposure | User awareness. |
2 | 2026.2.13 | SSRF, traversal, log poisoning; 0o600 cred permissions | Code-level fixes. |
3 | 2026.2.19 | Auto-generated tokens; audit flags; skill doc sanitization | Secure defaults. |
4 | 2026.2.21 | Browser sandbox; prototype pollution; environment injection; Docker isolation | Exploit containment. |
5 | 2026.2.22–2.24 | Obfuscation detection; PATH enforcement; cross-channel isolation | Anti-evasion. |
6 | 2026.2.25–2.26 | Immutable execution plans; secrets workflow; WebSocket auth; device pinning | Deep boundary enforcement. |
7 | 2026.3.1–3.7 | SecretRef 64 targets; plugin HTTP auth; hook injection policy; prompt-spoof neutralization | Ecosystem hardening. |
8 | 2026.3.12–3.13 | Unicode spoofing; wrapper smuggling; WebSocket hijacking; scope bleed; plugin auto-load block; webhook brute-force prevention | Semantic gap triage. Closing parsing discrepancies. |
The trajectory: Phases 1–6 built the security controls. Phase 7 extended them to the ecosystem. Phase 8 is discovering that the controls themselves are only as reliable as the parser’s fidelity to the operating system’s interpretation of the same input. Unicode characters, wrapper scripts, and scope declarations create gaps between what the control checks and what the system does. This phase is closing those gaps, one GHSA at a time.
This is the deepest layer of the reactive security model. The adversary’s creativity now targets not the system’s boundaries but the representation discrepancies between the layers that enforce those boundaries. Each fix is a specific answer to a specific discrepancy. Each new discrepancy requires a new fix. The cycle is structurally unbounded.
“You cannot packet-inspect an idea.”
AI SAFE² vs. OpenClaw 2026.3.12–3.13: The Difference Maker
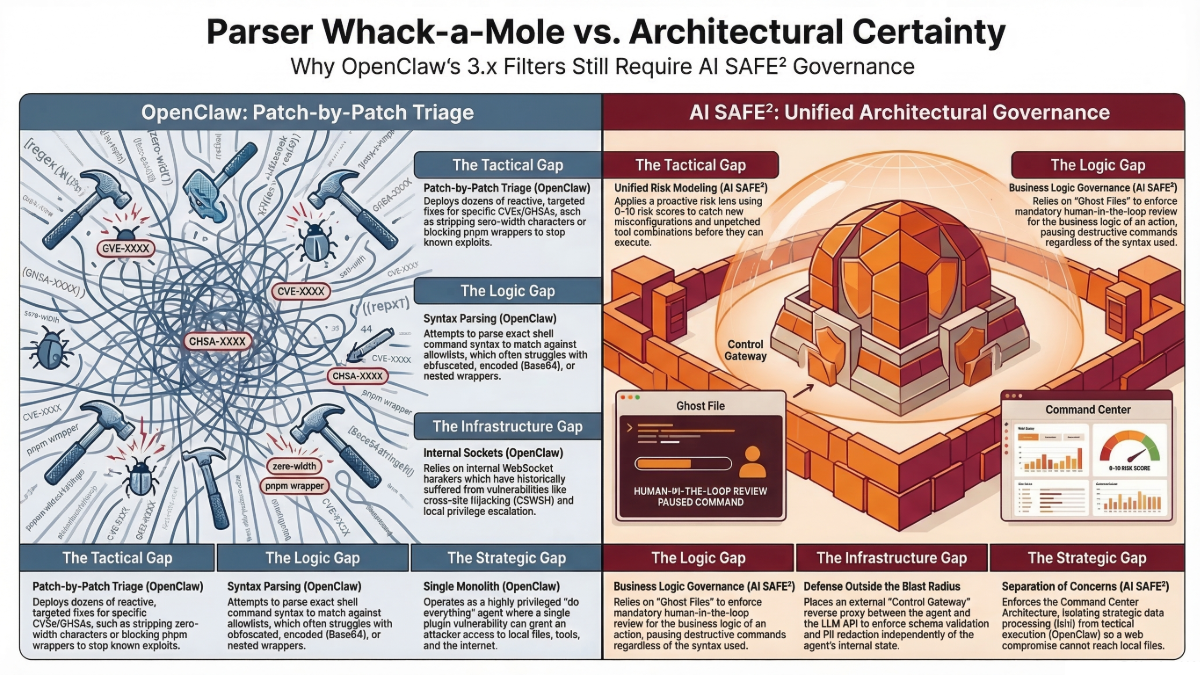
These releases are a masterclass in vulnerability triage. They also crystallize the fundamental limitation of parser-level defense: it is an enumeration problem with an unbounded search space.
A. Parser Triage vs. Behavioral Governance (Ghost Files)
OpenClaw (3.12–3.13 — The Patch): Escapes invisible Unicode in approval prompts. Normalizes compatibility code points before obfuscation checks. Unwraps pnpm, npm exec, Perl -M, and PowerShell -EncodedCommand to evaluate inner payloads against approval bindings. Each fix addresses a specific parsing discrepancy between display, evaluation, and execution.
AI SAFE² (The Architecture): Deploys Ghost Files to govern the action’s outcome, not its syntax. The Ghost File does not parse the command string. It evaluates what the action will do to real data, real systems, and real users, then pauses for human review. Whether the destructive payload arrived via clean ASCII, zero-width Unicode, or a PowerShell encoded wrapper is irrelevant to the Ghost File—the destruction is what triggers the gate.
The Difference: OpenClaw is playing an enumeration game: for each new encoding, each new wrapper, each new Unicode trick, a new parser rule is required. The adversary’s search space is unbounded. AI SAFE² constrains the outcome regardless of the encoding. One approach races to catalog every representation. The other makes the representation irrelevant. Detection is a strategy of hope. Certainty is a strategy of engineering.
“The Latency Gap: If the agent moves faster than the oversight, the system is ungoverned.”
B. Internal WebSocket Fixes vs. Positional Defense (Control Gateway)
OpenClaw (3.12–3.13 — The Patch): Shipped a critical fix (GHSA-5wcw-8jjv-m286) for cross-site WebSocket hijacking that could grant untrusted origins operator.admin access regardless of proxy headers. Shortened pre-auth handshake retention. Rejected oversized pre-auth frames. Capped device-token scopes. Cleared client-declared scope inflation on shared-token connections.
AI SAFE² (The Architecture): Deploys the Control Gateway as an external reverse proxy between OpenClaw and the LLM API. The Gateway enforces authentication, PII blocking, JSON schema validation, and spend-based Circuit Breakers independently of OpenClaw’s internal WebSocket or API listener. If OpenClaw’s gateway is compromised through a novel WebSocket vector, the external Gateway still mediates all outbound traffic.
The Difference: OpenClaw has now patched WebSocket hijacking vulnerabilities in 2.25, 3.1–3.7, and 3.13. Three release cycles addressing the same attack class. Each fix is correct. Each fix arrived after the vulnerability was exploitable. AI SAFE²’s Gateway does not depend on OpenClaw’s internal WebSocket implementation being correct—it enforces policy at a position the attacker cannot reach from inside the agent. If governance is not enforced at runtime, it is not governance. It is forensics.
C. Scope Capping vs. Architectural Isolation (Command Center)
OpenClaw (3.12–3.13 — The Patch): Caps device-token scopes to approved baselines. Clears self-declared elevated scopes. Blocks plugin auto-loading from cloned repos. Enforces session-tree visibility guards. Each fix constrains privilege escalation within the monolithic agent runtime.
AI SAFE² (The Architecture): Enforces the Command Center Architecture: Ishi (local, private, strategic) is physically separated from OpenClaw (remote, networked, tactical). A scope-bleed vulnerability that grants admin access within OpenClaw cannot reach Ishi’s private data because the two runtimes are on different machines.
The Difference: Scope capping constrains what a compromised session can do inside the agent. Architectural isolation ensures that even a fully compromised agent cannot reach the crown jewels. One is defense in depth. The other is defense in distance. Never build an engine you cannot kill.
D. GHSA-by-GHSA Triage vs. Unified Risk Modeling
OpenClaw (3.12–3.13 — The Patch): Deploys targeted fixes for over a dozen specific GHSAs. Each advisory addresses one parsing discrepancy, one scope vector, one webhook bypass. The fixes are individually correct and collectively impressive.
AI SAFE² (The Architecture): Applies a unified risk lens (0–10 risk scores for actions, 0–100 installation risk) that evaluates behavior patterns rather than individual syntax vectors. A novel encoding that bypasses OpenClaw’s parser but produces a high-risk action pattern still triggers the risk model. The Unified Audit Log provides immutable, ISO 42001 / SOC 2 mapped evidence for every scored event.
The Difference: GHSA-by-GHSA triage is necessary but structurally reactive. Each fix addresses a specific vector that existed before the patch. AI SAFE²’s risk model catches novel vectors that produce known dangerous patterns—even patterns that have never been individually patched. One is a catalog. The other is a classifier. Safety can be automated. Legal standing cannot.
“Policy is just intent. Engineering is reality.”
Control Mapping: OpenClaw 2026.3.12 – 2026.3.13 vs. AI SAFE²
Security Domain | OpenClaw 3.12–3.13 (Native) | AI SAFE² (External Enforcement) |
Exec Semantic Gap | Unicode spoofing escaped in prompts; compatibility normalization before heuristics; wrapper smuggling (pnpm/npm/Perl/PowerShell) unwrapped and inner payloads evaluated. | Ghost File protocol governs action outcomes regardless of encoding, wrapper, or syntax. Human review triggered by destructive intent, not command representation. |
WebSocket / Gateway | Browser origin validation for all connections regardless of proxy headers (GHSA-5wcw); pre-auth DoS defense; oversized frame rejection. | Control Gateway enforces auth, PII blocking, and egress policy as external reverse proxy. Not dependent on agent’s internal WebSocket implementation. |
Scope / Privilege | Device-token scope capping; client-declared scope clearing; Docker credential leak prevention. | Command Center Architecture: physical air-gap between private data (Ishi) and tactical executor (OpenClaw). Scope compromise contained to tactical layer. |
Plugin / Workspace | Plugin auto-load blocked for cloned repos; browser profile routes admin-only; sandbox session-tree visibility enforced. | TOOLS.md air-gap separates configs from behavioral instructions. Memory Vaccine treats all skill inputs as untrusted. SOUL.md resists identity redefinition. |
Webhook Auth | Feishu/Lark dual-key enforcement; LINE/Zalo signature required for empty probes; brute-force rate limiting on secret guesses. | Gateway validates all inbound payloads against schema. Circuit Breakers trigger on anomalous ingress. Immutable log of all webhook events. |
Compliance | Audit tool findings. No ISO 42001 / SOC 2 evidence generation. | Unified Audit Log: immutable, risk-scored (0–10), ISO 42001 / SOC 2 mapped. SIEM integration. Compliance-ready evidence. |
The Enumeration Ceiling: Why Cataloging Discrepancies Cannot Outpace Creating Them
OpenClaw releases 3.12 and 3.13 are monumental vulnerability cleanup. Over a dozen coordinated GHSA closures addressing invisible Unicode spoofing, wrapper smuggling, cross-site WebSocket hijacking, scope inflation, plugin auto-execution, and webhook brute-forcing. The depth and coordination of this triage is exceptional.
It also exposes the structural ceiling of parser-level defense. Each GHSA addresses a specific discrepancy between what the security control interprets and what the system does. Invisible characters. Wrapper scripts. Scope declarations. Encoding tricks. Each is a point in an unbounded search space of representation discrepancies. The adversary needs to find one. The defender needs to enumerate all of them.
“You cannot audit a millisecond with a weekly meeting.”
Eight phases of security maturation—from user warnings to semantic gap triage—have brought OpenClaw to the most fundamental constraint of reactive security: the defense must be correct about everything; the attacker needs to be creative about one thing.
The AI SAFE² Framework exists to break this asymmetry. It does not attempt to enumerate representation discrepancies. It governs outcomes. The Ghost File does not care whether the destructive command was encoded in ASCII, zero-width Unicode, or a PowerShell wrapper—it catches the destruction. The Control Gateway does not care which WebSocket vector the attacker used—it mediates all traffic from outside the agent. The Command Center does not care which scope-bleed technique granted admin access—it ensures admin access to the tactical layer cannot reach the strategic data.
The standard is clear: OpenClaw is cataloging discrepancies. AI SAFE² constrains consequences. One is an encyclopedia. The other is a wall.
“Milliseconds beat committees.”
Recommended Action
Immediate: Apply OpenClaw 3.12 and 3.13. The WebSocket hijacking fix (GHSA-5wcw-8jjv-m286) in 3.13 is critical—it addresses operator.admin escalation from untrusted browser origins. Verify plugin auto-loading is disabled for all cloned repositories.
Next: Run the AI SAFE² Scanner to verify the scope-capping and WebSocket origin changes have not disrupted your pairing topology. Test Unicode normalization against your custom exec allowlist entries to confirm no regressions.
Strategic: Deploy the AI SAFE² Control Gateway for positional egress enforcement that does not depend on parser fidelity. Implement Ghost Files for behavioral governance that is encoding-agnostic. Deploy the Command Center Architecture for physical isolation that survives scope compromise. Until these layers exist, your security depends on the parser being correct about every possible representation of every possible input. That is a bet against creativity.
Download the AI SAFE² Toolkit for OpenClaw
Schedule a Threat Exposure Assessment
Previous in Series: 3.1–3.7 | 2.25–2.26 | 2.22–2.24 | 2.21 | 2.19 | 2.13 | 1.29 & 2.1
FAQ: OpenClaw 2026.3.12–3.13 Security Upgrades and AI SAFE² Governance
17 questions practitioners are asking about these releases and what they mean for agentic AI security.
1. What is the “semantic gap” that these releases address?
The semantic gap is the discrepancy between three different interpretations of the same input: what the human sees in the approval prompt, what the parser evaluates against the allowlist, and what the operating system actually executes. Invisible Unicode characters, wrapper scripts, and encoding tricks create situations where these three interpretations diverge. A command that appears safe in the approval UI, passes the allowlist check, but executes a destructive payload exploits this gap. Releases 3.12 and 3.13 close specific instances of this divergence through Unicode escaping, compatibility normalization, and wrapper unwrapping.
2. What is invisible character spoofing (GHSA-pcqg-f7rg-xfvv)?
Invisible Unicode formatting characters—zero-width joiners (U+200D), zero-width spaces (U+200B), right-to-left marks (U+200F), and similar code points—render as nothing in most display contexts but are present in the underlying string. An attacker could insert these characters into a shell command, making the approval prompt display a benign command while the actual string contained hidden characters that altered execution behavior. The fix escapes these characters so they render visibly in approval prompts, closing the gap between what the human sees and what the string contains.
3. What is wrapper smuggling and which wrappers are addressed?
Wrapper smuggling exploits the fact that allowlist checks evaluate the outer command (the wrapper) rather than the inner payload it executes. An attacker wraps a blocked command inside an approved binary: pnpm exec, npm exec, Perl -M (module loader), or PowerShell -EncodedCommand. The allowlist sees the outer binary as permitted and approves execution. The inner payload—which may be a blocked destructive command—executes without independent evaluation. The fix unwraps these complex execution forms and evaluates the inner payload against the approval bindings. Three separate GHSAs cover different wrapper families.
4. What is the critical WebSocket hijacking fix in OpenClaw 2026.3.13 (GHSA-5wcw-8jjv-m286)?
This is the third WebSocket hijacking fix in the series, following the ClawJacked vulnerability patch in 2.25 and continued hardening in 3.1–3.7. The 3.13 fix enforces browser origin validation for all browser-originated connections regardless of proxy headers. Previous fixes validated origin but could be bypassed when connections passed through proxies that stripped or spoofed the Origin header. An untrusted browser origin exploiting this path could obtain operator.admin access—full control of the agent—from any website. The fix validates origin independently of proxy-provided headers.
5. What is token scope bleed (GHSA-2pwv-x786-56f8, GHSA-rqpp-rjj8-7wv8)?
Token scope bleed occurs when a connection claims more permissions than it was granted. In two variants: first, issued device-tokens could carry scopes beyond the paired device’s approved baseline, giving the device more access than intended. Second, a device-less operator connecting via a shared token could self-declare elevated scopes in the WebSocket handshake—effectively requesting admin access and having it granted because the system trusted the client’s scope declaration. The fixes cap issued scopes to the approved baseline and clear unbound client-declared scopes on shared-token connections.
6. Why is plugin auto-loading from cloned repositories dangerous (GHSA-99qw-6mr3-36qr)?
When a developer clones a repository that contains a workspace plugin directory, OpenClaw previously auto-loaded and executed the plugin code without asking for permission. An attacker could create a repository with a malicious workspace plugin, share it through any channel—GitHub, documentation links, community forums—and compromise any developer who cloned it. The fix disables implicit auto-loading, requiring an explicit trust decision before workspace plugin code executes.
7. How does AI SAFE²’s Ghost File address Unicode spoofing without parsing Unicode?
The Ghost File does not parse command syntax at all. It evaluates the action’s outcome: what data will be modified, what files will be deleted, what messages will be sent. Whether the command that triggers the deletion was encoded in clean ASCII, zero-width Unicode, or a PowerShell encoded wrapper is irrelevant—the Ghost File detects the destructive outcome and pauses for human review. This is why behavioral governance survives encoding tricks: it operates on consequences, not representations.
8. What is the session-tree visibility fix (GHSA-wcxr-59v9-rxr8)?
OpenClaw supports sandboxed sub-agents that execute tasks with restricted permissions. Before this fix, a sandboxed sub-agent could inspect the parent agent’s session metadata, including conversation history, credentials, and operational context. A compromised sub-agent could harvest this information to escalate its capabilities or exfiltrate sensitive data. The fix enforces visibility boundaries: sandboxed sub-agents can only see their own session tree, not the parent’s.
9. What are the Feishu/Lark webhook fixes and what attack did they prevent?
Two separate vulnerabilities: First, webhook mode accepted events verified only by verificationToken without requiring encryptKey. An attacker who obtained or guessed the verification token could forge webhook events. The fix requires both keys. Second, typing lookup behavior allowed group authorization bypass via person-to-person reactions—an attacker could trigger agent behavior through p2p reactions that bypassed group-level authorization checks. The fix preserves typing lookup to maintain correct authorization evaluation.
10. Why has WebSocket hijacking required fixes across three separate release cycles?
WebSocket hijacking is not a single vulnerability but an attack class with multiple variants. Release 2.25 addressed the original ClawJacked vulnerability where localhost connections bypassed rate limiting. Releases 3.1–3.7 hardened origin checks and added Permissions-Policy headers. Release 3.13 addresses bypass via proxy header stripping. Each variant exploits a different aspect of the same fundamental challenge: validating the true origin of a WebSocket connection when intermediaries can modify headers. This pattern illustrates why positional defense (AI SAFE²’s Gateway) is structurally superior to iterative origin validation fixes.
11. What is the LINE/Zalo empty-event probe attack?
Attackers send empty POST bodies to webhook endpoints to determine whether the endpoint is active and responsive. Without signature verification on empty events, the attacker learns which endpoints are live without triggering content validation or logging meaningful audit data. Once an active endpoint is identified, the attacker can focus brute-force or targeted exploitation efforts. The fix requires valid signatures even for empty-event probes, eliminating this reconnaissance technique.
12. How does the Unicode normalization fix interact with custom exec allowlists?
The fix strips invisible formatting code points and normalizes compatibility Unicode before obfuscation checks run. If an operator has custom allowlist entries that inadvertently contain compatibility Unicode characters, the normalization may change how those entries match. Operators should test their custom allowlist entries after applying the update to confirm no regressions. This is a case where security correctness may require allowlist maintenance.
13. What are the eight phases of OpenClaw’s security maturity model?
Phase 1: User awareness. Phase 2: Code-level fixes. Phase 3: Secure defaults. Phase 4: Exploit containment. Phase 5: Anti-evasion. Phase 6: Deep boundary enforcement. Phase 7: Ecosystem hardening. Phase 8: Semantic gap triage—closing the parsing discrepancies between what the security control checks and what the operating system executes. Each phase addresses a higher-order threat class, and Phase 8 represents the most fundamental layer: ensuring the controls built in previous phases interpret input identically to the execution environment.
14. Why does Microsoft recommend treating OpenClaw agents as untrusted code execution?
Microsoft’s Security Blog explicitly recommends deploying OpenClaw only in fully isolated environments with dedicated, non-privileged credentials and access only to non-sensitive data. Their assessment is that OpenClaw’s runtime ingests untrusted text, downloads and executes skills from external sources, and performs actions using assigned credentials—effectively shifting the execution boundary from static code to dynamically supplied content without equivalent controls around identity, input handling, or privilege scoping. This aligns precisely with AI SAFE²’s Command Center Architecture: isolating the tactical executor from sensitive data and strategic decisions.
15. What compliance gaps remain after the OpenClaw 2026.3.12 – 3.13 releases?
OpenClaw’s GHSA triage is engineering-grade vulnerability management. It does not produce compliance evidence. There is no immutable audit log with risk scores, no authorization attribution per action, no policy conformance reporting, and no SIEM integration. For organizations subject to ISO 42001, SOC 2, HIPAA, or financial regulation, the gap between parser-level defense and compliance readiness is the gap between engineering confidence and legal defensibility. AI SAFE²’s Unified Audit Log bridges this gap.
16. How should I sequence the 3.12–3.13 updates with AI SAFE² deployment?
Apply 3.13 first—the WebSocket hijacking fix is critical. Then apply 3.12 for the Unicode and wrapper smuggling fixes. Verify plugin auto-loading is disabled. Run the AI SAFE² Scanner to check scope-capping changes and test Unicode normalization against custom allowlists. Deploy the Control Gateway for positional egress enforcement. Implement Ghost Files for behavioral governance. Deploy the Command Center for physical isolation. Each layer addresses a different structural limitation that parser triage cannot.
17. What is the most important insight from the 3.12–3.13 releases?
OpenClaw has reached the semantic gap frontier: the point where security depends on the parser interpreting every possible representation of every possible input identically to the operating system. This is a structurally unbounded problem. The adversary needs to find one discrepancy. The defender needs to enumerate all of them. That asymmetry is the fundamental constraint of parser-level defense and the fundamental reason external governance exists. AI SAFE² does not enumerate representations. It constrains consequences. One is an encyclopedia that must be complete. The other is a wall that must be present.