OpenClaw Security Upgrades 2026.3.23-4.12 – AI SAFE² Analysis
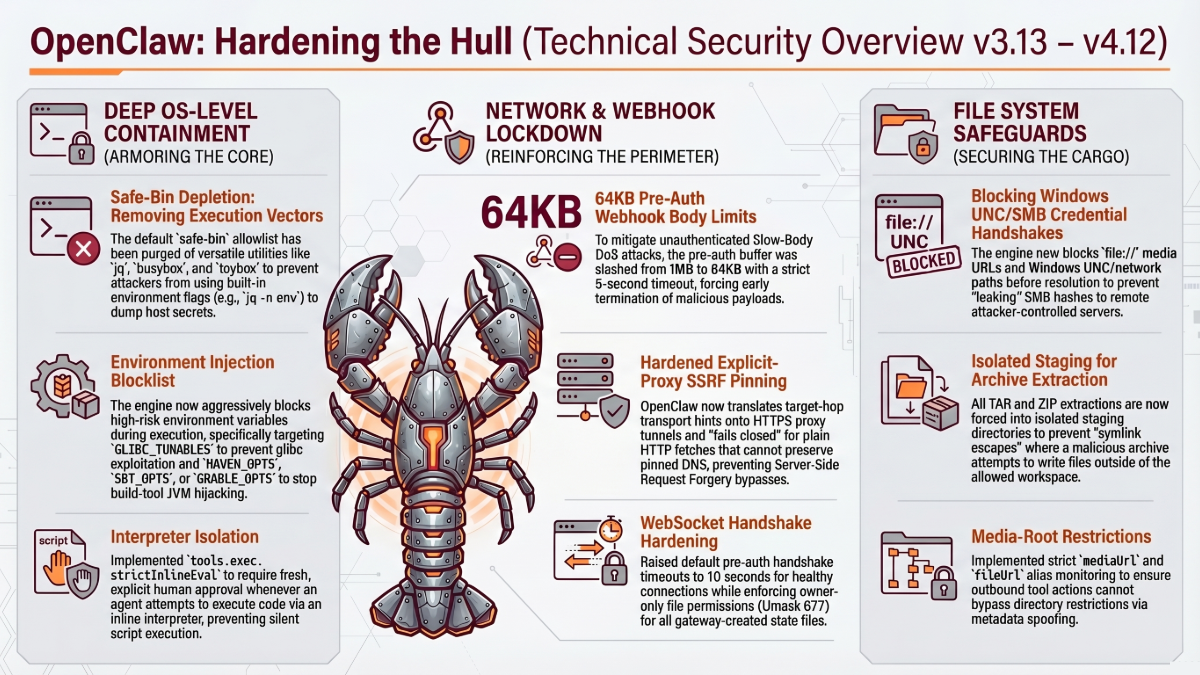
OpenClaw 2026.3.23 to 4.12 Security Upgrades From Deep OS Containment to Privilege Escalation Defense – Analyzed Against AI SAFE² AI SAFE² SECURITY […]
AI Governance Maturity Model Comparison on Frameworks & Governance AI Maturity
AI Governance Maturity Models: AISM vs. The Field Real Controls That Generate Real Effects vs. Paper Policy Drills The AI governance landscape […]

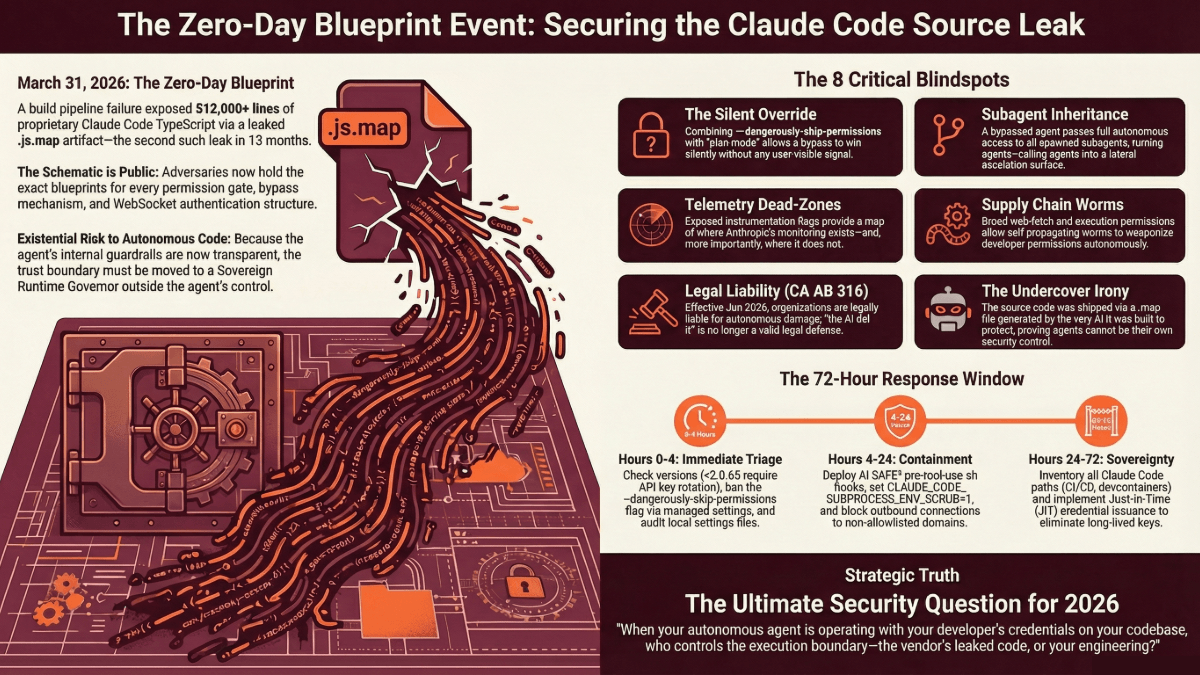
OpenClaw Security Upgrades 2026.3.12–3.13 – AI SAFE² Analysis
OpenClaw 2026.3.12 & 3.13 Security Upgrades AI SAFE² SECURITY ANALYSIS OpenClaw 2026.3.12 & 3.13 Security Upgrades From Ecosystem Hardening to Semantic Gap […]
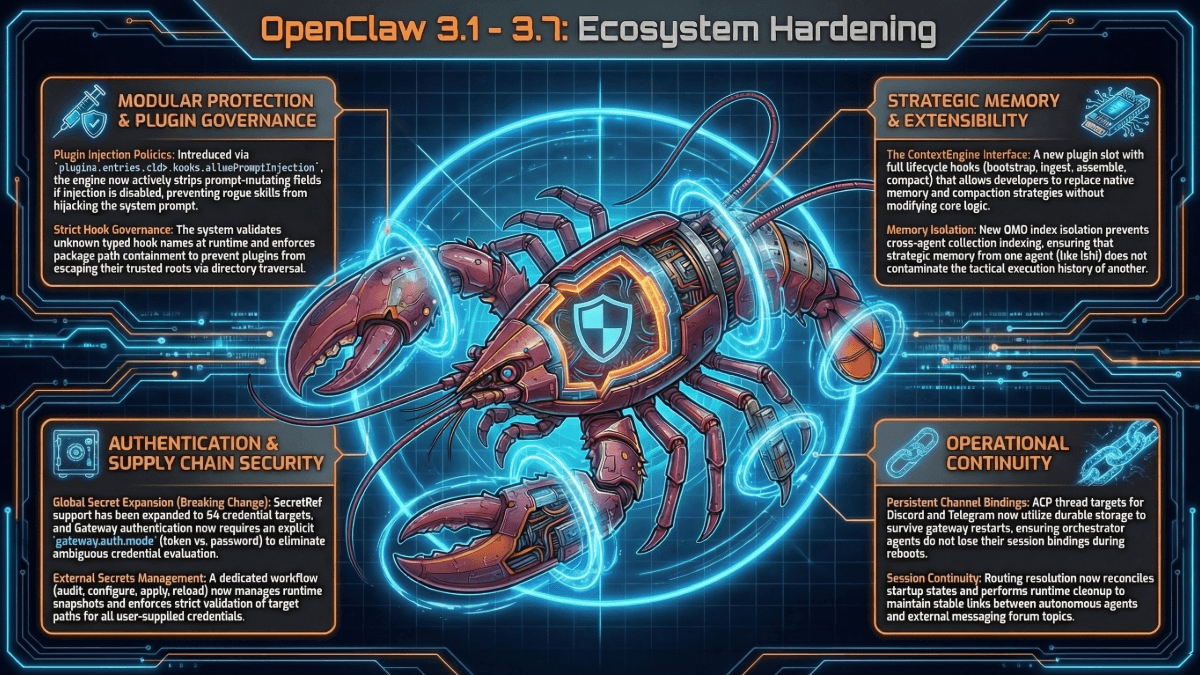
OpenClaw Security Upgrades 2026.3.1 – 3.7
OpenClaw Security Upgrades 2026.3.1 – 3.7 AI SAFE² SECURITY ANALYSIS From Deep Boundary Enforcement to Ecosystem Hardening — Analyzed Against AI SAFE² […]

OpenClaw Security Upgrades 2026.2.25 to 2.26
New OpenClaw 2026.2.25 & 2.26 Security Upgrades From Anti-Evasion to Deep Boundary Enforcement -> Analyzed Against AI SAFE² Series: OpenClaw Security Upgrades […]

OpenClaw Security Upgrades 2026.2.22 – 2.24 – Analyzed Against AI SAFE²
OpenClaw 2026.2.22 – 2.24 Security Upgrades AI SAFE² SECURITY ANALYSIS From Exploit Containment to Anti-Evasion -> Analyzed Against AI SAFE² Series: OpenClaw […]

OpenClaw Security Upgrades 2026.2.21 – Analyzed Against AI SAFE²
OpenClaw Security Upgrades 2026.2.21 AI SAFE² SECURITY ANALYSIS OpenClaw Security Upgrades 2026.2.21 From Auto-Remediation to Exploit Containment — Analyzed Against AI SAFE² […]

OpenClaw Security Upgrade 2026.2.19 – AI SAFE² Analysis on Securing Your AI Agent
The Third Phase: When the System Stops Asking and Starts Enforcing AI SAFE² SECURITY ANALYSIS OpenClaw Security Upgrades 2026.2.19 From Granular Hardening […]
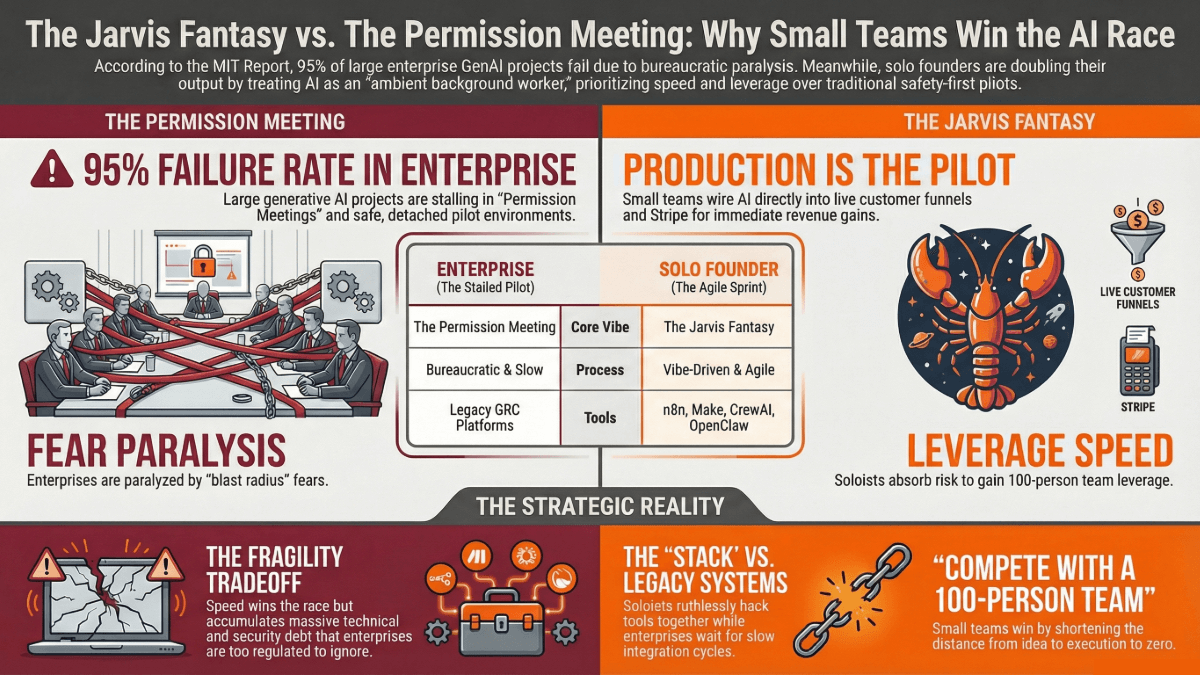
Enterprise AI Failure vs Solo Founders Generative AI Project Advantage
Enterprise AI Failure vs Solo Founders Spirit The Jarvis Fantasy vs. The Permission Meeting: Why Small Teams are Winning the Agentic AI […]

OpenClaw Security Upgrade 2026.2.13 – AI SAFE² Analysis
OpenClaw Security Upgrades 2026.2.13 AI SAFE² SECURITY ANALYSIS From Feature Expansion to Granular Hardening -> Analyzed OpenCLaw Security Upgrade 2026.2.13 Against AI […]

OpenClaw Security Upgrades – Latest Security Updates Analyzed Against AI SAFE²
OpenClaw Security Upgrades Compared Against AI SAFE² The “Patch vs. Policy” Dilemma: Why Code Fixes Aren’t Enough for Agentic AI In the […]