The MCP Supply Chain Crisis Is Worse Than the Headlines Say
Framework Reference: AI SAFE2 v3.0 CP.5.MCP
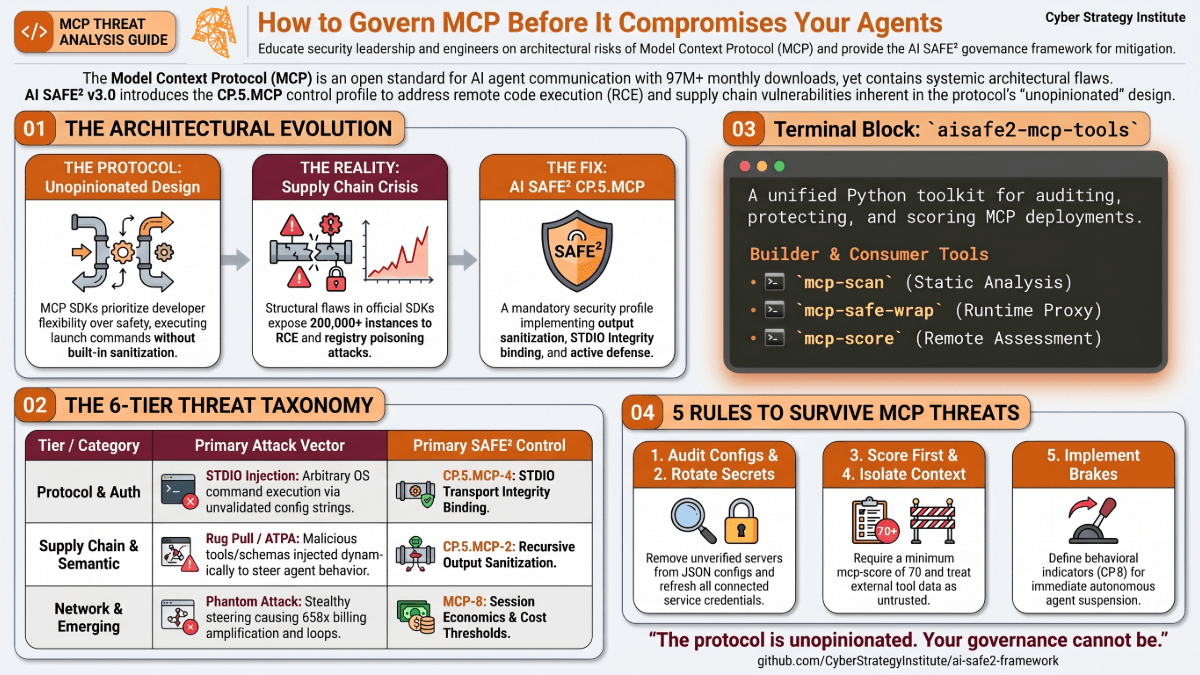
Executive Summary
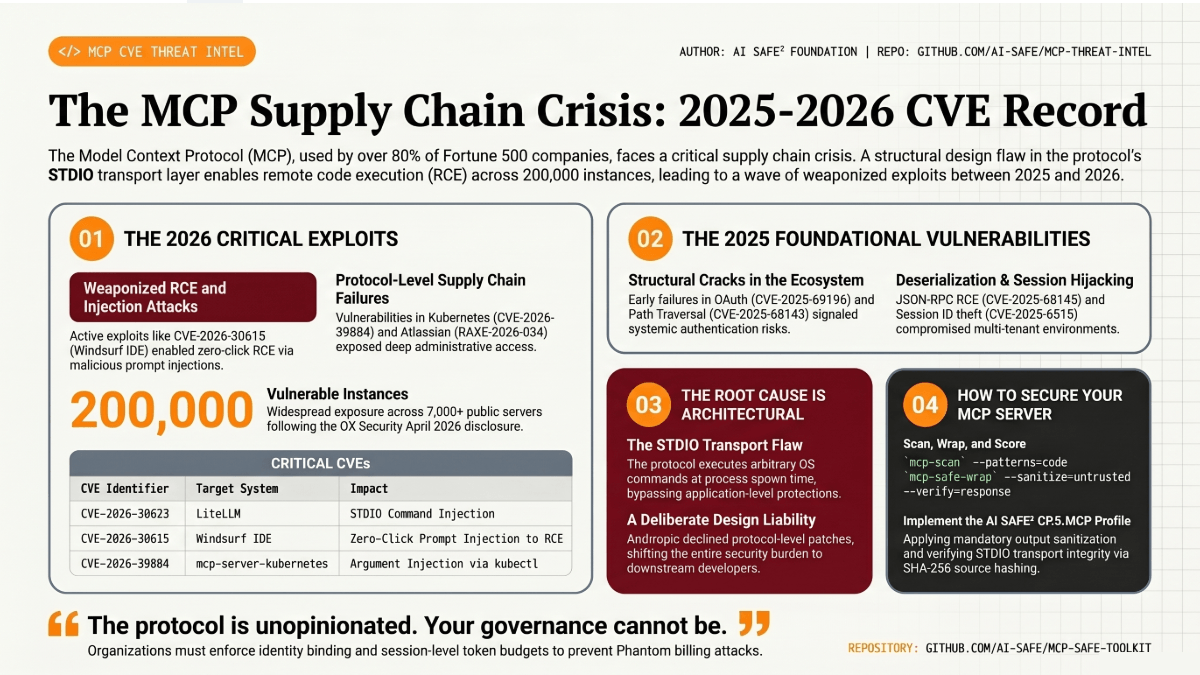
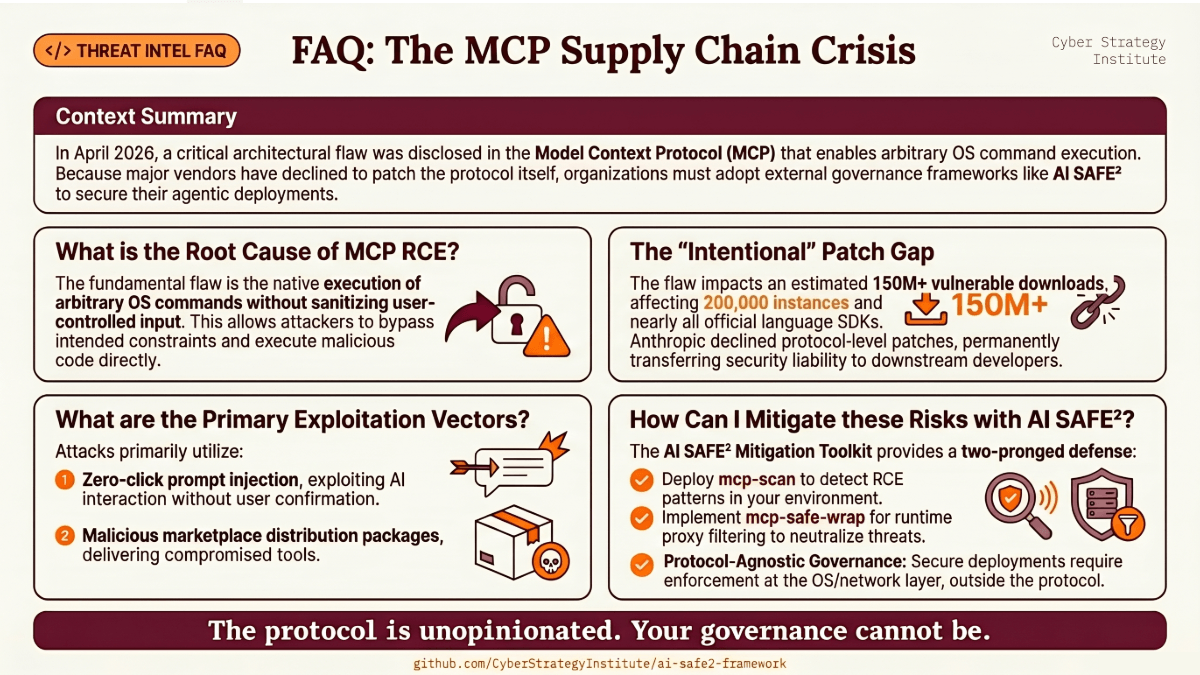
The Model Context Protocol (MCP), Anthropic’s open standard for AI agent communication, has emerged as the most consequential attack surface in the 2026 agentic AI ecosystem. A landmark April 2026 disclosure by OX Security confirmed that an architectural flaw baked into official MCP SDKs across Python, TypeScript, Java, and Rust exposes over 150 million downloads, 7,000 publicly accessible servers, and up to 200,000 total vulnerable instances to remote code execution, is a systemic MCP security flaw. Anthropic has formally declined to patch the root cause at the protocol level, creating a supply chain crisis. This is not an isolated CVE. It is a systemic design liability that cascades through every downstream framework, IDE, and production deployment that trusted the reference implementation.
Key findings: The OX STDIO RCE vulnerability is a supply chain event, not a point vulnerability. Every language SDK inherited the same architectural choice. Nine of eleven MCP registries were successfully poisoned during OX testing. SSRF vulnerabilities affect over 36.7% of analyzed MCP servers. The Phantom API billing amplification attack achieves 658x cost amplification with a 97% miss rate from standard defenses. Multi-agent lateral movement via MCP occurs without detectable anomalies at the per-agent level, requiring inter-agent edge detection. CSI Research Note 023 covered the primary threat classes but missed four material threat categories: MCP-as-C2 (Swarm C2), Parasitic Toolchain / MCP-UPD, API billing amplification, and post-update privilege persistence.
This analysis provides a comprehensive multi-stakeholder threat model covering protocol designers, MCP server operators, tool developers, AI orchestration engineers, enterprise consumers, and federal/DoD deployers. It concludes with enhanced control recommendations mapped to AI SAFE2 v3.0 CP.5 and aligned to NIST SP 800-53 Rev 5, CIS Controls v8.1, and CMMC 2.0/FedRAMP requirements.
The headlines called it a critical vulnerability. That framing is wrong, and the understatement is dangerous.
What OX Security documented in April 2026 is not a vulnerability. It is a structural governance failure baked into the design of a protocol that now underpins the productivity workflows of over 80% of Fortune 500 companies. The distinction matters because vulnerabilities get patched. Design failures get inherited by every library, every framework, every IDE extension, and every enterprise deployment that trusted the reference implementation.
Anthropic confirmed the behavior is intentional. They declined the patch. The responsibility for every downstream consequence has been formally transferred to developers who built on a foundation they were never told was structurally unsound.
Protocol Architecture and Its Trust Model
MCP defines a client-host-server architecture in which an MCP Host (Claude Desktop, Cursor, Windsurf) operates an MCP Client that connects to one or more MCP Servers exposing Tools, Resources, and Prompts to the AI model. The protocol operates over two primary transport mechanisms: STDIO (standard input/output, for local process execution) and HTTP/SSE (server-sent events, for remote services). The security model assumes MCP servers are trusted entities. That foundational assumption is what attackers systematically exploit.
As of April 2026, only 8.5% of MCP servers use OAuth for authentication. The remainder rely on static API keys or no authentication at all. The MCP ecosystem is, in the words of NimbleBrain’s 2026 state-of-the-ecosystem analysis, where web security was in 2005: functional but immature. The Linux Foundation now governs the protocol, but adoption of the November 2025 OAuth 2.1 specification update remains the exception, not the rule.
What OX Security Found
On April 14 and 15, 2026, OX Security researchers published their landmark advisory detailing a critical architectural vulnerability in the MCP STDIO execution model. The core finding: the official MCP STDIO transport will execute any arbitrary operating system command to launch an MCP server. The command still runs even when the server startup fails. No sanitization warnings appear. No red flags exist in the developer toolchain.
The researchers executed commands on six live production platforms and issued ten or more High and Critical CVEs across widely-used projects. Critically, Anthropic declined to modify the protocol architecture, characterizing the STDIO execution model as expected behavior and placing sanitization responsibility on downstream developers. LangChain and Microsoft issued identical positions. This response represents a structural governance failure. The current implementation of MCP places the entire burden of security on downstream developers, a design that guarantees vulnerability at scale.
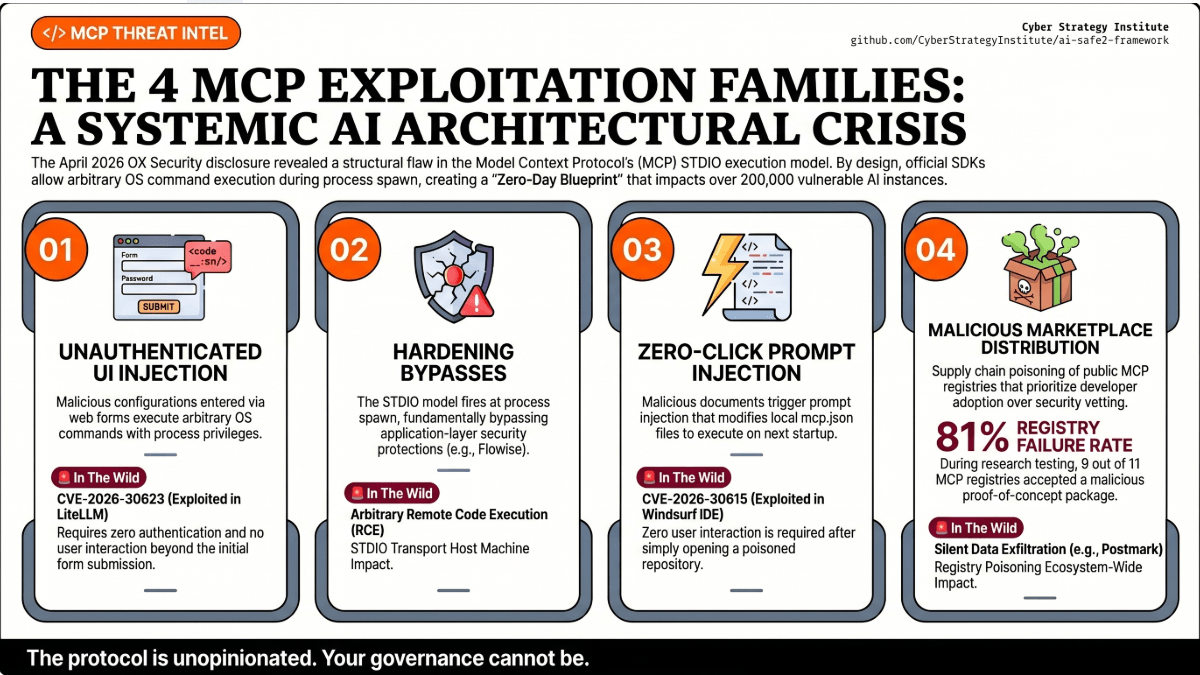
The Four Exploitation Families
OX Security’s research identified four distinct exploitation families, each requiring different defensive responses.
Unauthenticated UI Injection: A malicious MCP configuration entered through a web interface executes arbitrary OS commands with the privileges of the process. No authentication required. No interaction beyond form submission. CVE-2026-30623 is this pattern against LiteLLM.
Hardening Bypasses: Platforms that implemented surface-level protections still fell. Flowise had hardening. The hardening was bypassed. The STDIO model executes regardless of what sits in front of it because execution happens at process spawn time, not at request time.
Zero-Click Prompt Injection: In Windsurf IDE, a malicious document or web page triggers prompt injection through the IDE’s auto-processing of repository content. The injected payload modifies mcp.json, inserting a malicious STDIO entry that executes on next agent startup. Zero user interaction required after opening the repository. CVE-2026-30615.
Malicious Marketplace Distribution: The OX team tested 11 MCP registries by submitting a proof-of-concept malicious package. Nine of eleven accepted it. The September 2025 Postmark incident confirms this vector is not theoretical.
The Root Cause Is Not What the CVEs Say
The CVE model assigns identifiers to specific manifestations of a vulnerability. CVE-2026-30623 is LiteLLM. CVE-2026-30615 is Windsurf. But these CVEs do not share a common root cause at the library level or the product level. They share a root cause at the protocol level.
The fundamental problem: the MCP STDIO transport model was designed to be unopinionated. The protocol creators chose flexibility over safety guarantees. There is no opt-in to a safe mode. There is no manifest-only execution requirement. There is no allowlist enforcement at the SDK level. Developers building on the official reference implementation inherit maximum risk with no indication in the developer toolchain that anything is wrong.
Three protocol-level fixes were available and declined by Anthropic: manifest-only execution (a whitelist of permitted launch commands in a signed manifest), an explicit opt-in flag for dynamic STDIO arguments (creating a forcing function for security review), and mandatory SDK-level sanitization requirements. None were implemented. The burden was formalized as a developer responsibility. In a protocol with 150 million downloads and 200,000 deployment instances, that policy decision is not a security recommendation. It is a mass transfer of liability.
From the developer perspective, developers using official Anthropic SDK examples inherit this exposure by default. The dangerous behavior is the default behavior. Anthropic’s suggested remediation, treat external MCP configuration input as untrusted, shifts the entire burden to individual developers without providing enforcement mechanisms. From the protocol designer perspective, the deliberate choice to remain unopinionated about input handling creates a systemic liability at scale. Even if Anthropic sanitized the launch command, an attacker controlling both the command and the launched process can move malicious logic into the server itself, since the root tension is between protocol flexibility and security guarantees.
Comprehensive Threat Taxonomy
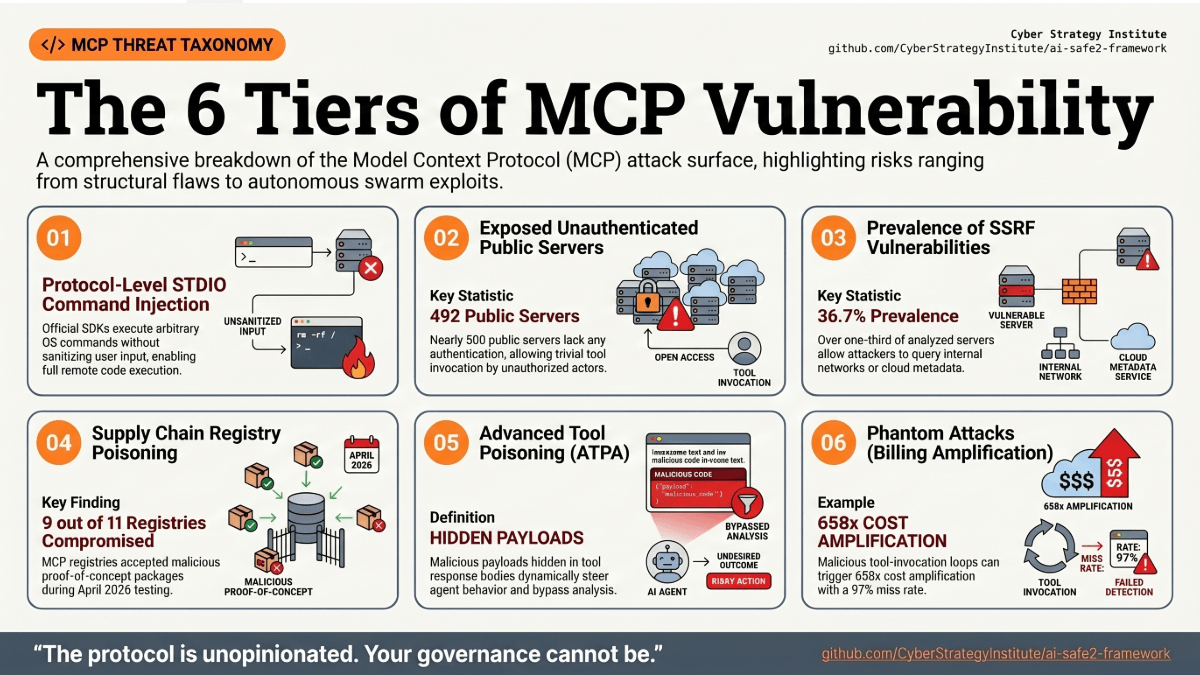
Tier 1: Protocol-Level Architectural Threats
T1.1 STDIO Command Injection is the root architectural flaw. Severity Critical, Exploitability Easy, Prevalence Universal. The STDIO transport model in all official MCP SDKs executes the configured launch command without sanitizing user-controlled input. Any pathway that allows user or external input to influence a StdioServerParameters configuration string results in arbitrary OS command execution. The attack requires no authentication, leaves no red flags in developer toolchains, and operates at the process level with the full privileges of the executing user.
T1.2 Token Passthrough represents an audience validation failure. Severity High, Exploitability Easy. MCP servers that forward client-supplied OAuth tokens to downstream APIs without validating the aud (audience) claim allow attackers to reuse tokens for unintended resource servers. This violates OAuth trust boundaries and enables token abuse across service boundaries. CVE-2025-69196 demonstrates that tokens obtained for one MCP server can be replayed against others in federated deployments.
T1.3 Session ID Exposure in URLs operates at Medium severity with Easy exploitability. MCP implementations frequently expose session identifiers in HTTP URL paths, enabling session hijacking by any party who observes the URL via referrer headers, proxy logs, browser history, or network interception.
Tier 2: Authentication and Authorization Threats
T2.1 Unauthenticated Server Access. Severity Critical, Exploitability Trivial, Prevalence Widespread. A July 2025 Trend Micro survey found 492 exposed MCP servers with no authentication or encryption. The Adversa AI Top 25 ranks unauthenticated access as Impact Score 9/10 with Trivial exploitability. Any tool invocation, resource read, or prompt execution can be performed by any network-accessible attacker.
T2.2 OAuth Confused Deputy and Consent Bypass. Severity Critical, Exploitability Moderate. CVE-2026-27124 (FastMCP) and the Square MCP server vulnerability demonstrate that MCP OAuth implementations routinely fail to bind authorization codes to user sessions, enabling CSRF-style attacks where a malicious link leaks an MCP authorization code to an attacker-controlled redirect_uri. Post-fix, clients registered before the patch remained vulnerable because redirect_uri restrictions only applied to newly registered clients.
T2.3 Privilege Abuse via Over-Permissioned Connectors. Severity Medium, Exploitability Easy, Prevalence Common. The GitHub MCP incident demonstrated that a single over-privileged Personal Access Token wired into an MCP server allowed a prompt-injected agent to exfiltrate private repository contents, internal project details, and personal financial information into a public pull request.
T2.4 Post-Update Privilege Persistence. Severity High, Exploitability Moderate. After MCP server updates, revoked or outdated privileges may persist due to revocation propagation failures. Attackers who identify this window can exploit residual access to conduct unauthorized actions that would otherwise be blocked.
Tier 3: Supply Chain and Ecosystem Threats
T3.1 Rug Pull Attack via Dynamic Schema Mutation. Severity High, Exploitability Easy, Prevalence Emerging. A legitimate-appearing MCP server is published, builds adoption, and passes developer review. The maintainer account is then compromised or the project is sold to a malicious actor. The server’s tools/list response is silently updated to include malicious instructions in tool descriptions. Because tool descriptions are loaded dynamically at runtime rather than at install time, no code review catches the change. The malicious schema change can instruct the AI agent to read private credentials or exfiltrate data while the underlying tool implementation remains functionally unchanged. Traditional static code review will not flag this attack because the payload lives in dynamic metadata sent at runtime.
T3.2 Typosquatting and Revival Hijack. Severity High, Exploitability Easy. MCP configurations are frequently copy-pasted from blog posts and documentation. A single-character typo silently downloads and executes attacker-controlled code on every agent startup. Revival hijack occurs when maintainers remove packages from PyPI or npm and the package name becomes available for re-registration. Supply chain attacks via package manager configurations require no interaction with the MCP protocol itself.
T3.3 Malicious Registry Poisoning. Severity High, Exploitability Easy, Prevalence Demonstrated. The OX September 2025 supply chain incident documented a malicious MCP server package masquerading as a legitimate Postmark MCP Server that injected BCC copies of all email communications to an attacker-controlled server. Nine of eleven MCP registries were successfully poisoned with a proof-of-concept package during OX’s April 2026 research.
Tier 4: AI-Specific Semantic Threats
T4.1 Tool Poisoning (TPA) and Full Schema Poisoning (FSP). Severity Critical, Exploitability Easy, Prevalence Universal. Originally documented by Invariant Labs in March 2025, tool poisoning embeds adversarial instructions in MCP tool descriptions that are invisible to users but injected directly into the AI agent’s context. The agent processes these as legitimate instructions and executes them. CyberArk’s research expanded this to Full Schema Poisoning (FSP), demonstrating that the attack surface extends across the entire tool schema, including parameter names, enum values, and response schemas, not just the description field. A poisoned tool does not need to run. Its description alone can steer behavior. MCPTox benchmark results demonstrate high success rates for tool poisoning across major commercial agents. OWASP ranked it as a top agentic risk for 2026.
T4.2 Advanced Tool Poisoning (ATPA) places malicious logic in dynamic tool output rather than static descriptions. The poisoned payload arrives in the tool response body and steers the agent’s next action, completely bypassing pre-deployment static analysis. This is the attack class that drives the Phantom billing amplification vector.
T4.3 Cross-Server Tool Shadowing. Severity Medium, Exploitability Moderate. When an AI agent connects to multiple MCP servers simultaneously, a malicious server can register a tool with the same name as a trusted server’s tool. Because MCP clients aggregate all tool descriptions into a unified context without server-level namespace isolation, the agent cannot distinguish which server provides which tool. The malicious tool intercepts calls intended for the legitimate tool and optionally forwards to the real tool to preserve the appearance of normal operation.
T4.4 Prompt Injection and Cross-Prompt Injection (XPIA). Severity Critical, Exploitability Trivial, Prevalence Universal. Prompt injection via MCP occurs when malicious content in external resources retrieved by MCP tools overrides agent instructions. XPIA attacks do not require direct user input. A malicious document processed through a file-reading MCP tool can redirect the agent to exfiltrate data, install persistence, or perform confused deputy attacks. The Supabase Lethal Trifecta demonstrated this against Cursor AI.
T4.5 MCP Unintended Privacy Disclosure and Parasitic Toolchain Attacks. Severity High, Exploitability Complex, Prevalence Emerging. Formalized by Zhao et al. in a September 2025 arXiv paper covering 12,230 tools across 1,360 servers, this attack class requires no direct victim interaction. The attack operates in three phases: parasitic ingestion of a malicious prompt planted in an external data source, privacy collection via covert tool invocations, and privacy disclosure to an attacker-controlled destination. Ninety-two point nine percent of MCP server categories can participate as attack capabilities in an MCP-UPD chain. Two root design flaws enable MCP-UPD: the absence of context-tool isolation (MCP does not separate untrusted external content from executable instructions) and the absence of least-privilege enforcement (once a toolchain is triggered, MCP grants overbroad access without constraining tool invocation scope).
Tier 5: Network and Infrastructure Threats
T5.1 Server-Side Request Forgery (SSRF). Severity High, Exploitability Moderate, Prevalence Widespread. BlueRock’s April 2026 analysis of 7,000 or more MCP servers found that over 36.7% have potential exposed SSRF vulnerabilities. MCP servers that make HTTP requests based on LLM-provided URLs can be tricked into accessing internal services, cloud metadata endpoints, or private networks. The Microsoft MarkItDown MCP server demonstrated an SSRF vulnerability that enables full AWS account takeover by querying the IMDSv1 metadata service. CVE-2026-26118 (Azure MCP Server), RAXE-2026-034 (mcp-atlassian) and other CVEs establish SSRF as a systemic vulnerability class across the MCP ecosystem. The mcp-atlassian SSRF chains directly into prompt injection: the attacker-controlled server response is cached and injected into the LLM context as if it were legitimate Atlassian data.
T5.2 Localhost Bypass, DNS Rebinding, and NeighborJack. Severity High, Exploitability Moderate. MCP servers bound to 0.0.0.0 expose their interfaces to all network addresses. DNS rebinding attacks allow a malicious web page to instruct a browser to make requests to localhost, bypassing same-origin policy and reaching locally bound MCP servers.
T5.3 Cross-Tenant Data Exposure. Severity Medium, Exploitability Complex. The June 2025 Asana MCP Server incident demonstrated that multi-tenant MCP deployments can expose data from one organization to another through logic flaws in access control. Asana disabled its MCP feature entirely for over two weeks while engineers resolved the vulnerability.
T5.4 Path Traversal and Sandbox Escape. Severity High, Exploitability Moderate. The August 2025 Anthropic Filesystem MCP Server vulnerabilities included sandbox escape and symlink bypass, enabling arbitrary file access and code execution outside intended directory boundaries. CVE-2025-68143 documents path traversal via insufficient path normalization in MCP Resource URI handling.
Tier 6: Novel and Emerging Threat Classes
T6.1 MCP as Command-and-Control Infrastructure (Swarm C2). Severity Critical, Exploitability Complex, Prevalence Emerging. Vectra AI’s February 2026 research demonstrated that MCP can be weaponized as a legitimate-appearing C2 fabric for offensive agent swarms. Traditional C2 frameworks produce detectable beaconing patterns. MCP-based C2 generates semantically ambiguous traffic that is indistinguishable from legitimate enterprise AI tool use. The architecture assigns specialized roles to individual agents (reconnaissance, exploit research, exfiltration), coordinates them via MCP, and recombines work products at machine speed. The Vectra research used the Anthropic API as the attacker, combining a malicious system prompt with a high-level task to drive full exploit chains including AMSI bypass and lateral movement in Kubernetes environments. If an enterprise is already deploying MCP for productivity agents, adversarial MCP tasking blends into the background. Incident response playbooks must account for compressed, machine-speed attack timelines.
T6.2 API Billing Amplification and Resource Exhaustion (Phantom Attack). Severity High, Exploitability Moderate, Prevalence Emerging. The Phantom framework (November 2025) and the Beyond Max Tokens paper (arXiv 2601.10955, January 2026) introduce a financially motivated attack class with no analogue in traditional security. A malicious MCP server embeds subtle steering instructions in tool response bodies, not in schema or tool descriptions, that cause the agent to repeatedly re-invoke tools, walk unnecessary tool chains, or trigger self-referential loops. Empirical results: 658x cost amplification, up to 26x API call inflation with 98% attack success rate across four leading enterprise frameworks, and a 97% miss rate from standard defenses. The attack is spec-compliant, schema-clean, and task-completing. The user receives a correct answer. The only signal is the API billing line item. Real-world precedent: four AI agents entered an infinite retry loop and generated a $47,000 API bill in 11 days.
T6.3 Multi-Agent Lateral Movement via Delegation Edges. Severity Critical, Exploitability Complex, Prevalence Emerging. In multi-agent orchestration systems, compromise propagates through delegation edges rather than individual agent compromise. The Cloud Security Alliance’s April 2026 analysis notes that in a compromised multi-agent chain, each individual agent still behaves normally but the chain connecting them is compromised. The attacker does not escalate privileges. The compromised agent passes attacker-controlled context, calls tools, and hands off to the next agent with no detectable anomaly at the per-agent level. ARMO’s research identifies three detection surfaces that per-agent sensors cannot cover: the delegation edge where compromise propagates between agents, the shared context and memory layer, and the orchestrator node routing between agents. MCP’s role in multi-agent architectures makes it the primary contagion channel.
T6.4 MCP Context Poisoning and Persistent Memory Injection. Severity High, Exploitability Moderate. Claude Code’s source code, inadvertently exposed via an unobfuscated package in March 2026, revealed that the agent runtime treats MCP tool results as trusted, persistent context without compression, decay, or guardrails. Once a poisoned tool result enters the agent’s persistent memory, subsequent agent behavior is influenced across all future interactions, not just the current session. Unlike prompt injection (which is bounded to the current context window), persistent memory injection creates a long-horizon behavioral manipulation channel. This is the poison the memory, not the prompt paradigm.
CVE Reference Index (2025 to 2026)
The following table documents the confirmed CVE record from the MCP threat landscape. Ten or more additional CVEs from the OX Advisory remain under coordinated disclosure as of April 27, 2026.
CVE | System | Attack Class | Status |
CVE-2026-30623 | LiteLLM | STDIO Command Injection | Patched |
CVE-2026-30615 | Windsurf IDE | Zero-Click Prompt Injection to STDIO RCE | Patched |
CVE-2026-39884 | mcp-server-kubernetes | Argument Injection via kubectl | Patched v3.5.0 |
CVE-2026-27124 | FastMCP OAuthProxy | OAuth Confused Deputy | Patched |
CVE-2026-26118 | Azure MCP Server | SSRF to Privilege Escalation | Patched |
CVE-2026-25536 | Generic MCP Server | Cross-Client Data Leak | Varies |
CVE-2025-69196 | FastMCP OAuth | OAuth Token Cross-Server Reuse | Patched |
CVE-2025-68145 | Multiple MCP Frameworks | JSON-RPC Deserialization RCE | Varies |
CVE-2025-68143 | MCP Resource URIs | Path Traversal | Varies |
CVE-2025-68144 | MCP OAuth Clients | Token Leakage in Callback | Varies |
CVE-2025-6514 | STDIO Mode Servers | Command Injection via Tool Parameters | Varies |
CVE-2025-6515 | oatpp-mcp | Prompt Hijacking / Session ID Theft | Patched |
CVE-2025-6607 | mcp-browser-agent | SSRF via URL Parameters | Patched |
CVE-2025-6470 | google-search-mcp | SSRF via extractContent() | Patched |
RAXE-2026-034 | mcp-atlassian | SSRF to Prompt Injection Chain (CVSS 8.2) | Patched |
Real-World Incidents and Breach Timeline
Date | System | Incident | Root Cause | Impact |
Mar 2025 | GitHub via MCP | Prompt-injected agent exfiltrated private repo contents and salary data into a public pull request | Over-privileged PAT plus untrusted content in LLM context | Data exposure, reputational harm |
Jun 2025 | Asana MCP Server | Cross-tenant data leakage: Organization A data visible to Organization B agents | Logic flaw in multi-tenant access control | MCP feature disabled for 2 weeks |
Jul 2025 | Amazon Q (VS Code) | Agent wiped local filesystem and deleted AWS resources after PR-embedded malicious prompt | Untrusted input plus destructive capability with no external comms required | System wipe, cloud resource deletion |
Aug 2025 | Anthropic Filesystem MCP | Sandbox escape and symlink bypass enabling arbitrary file access and code execution | Poor sandbox implementation, insufficient directory containment | Host filesystem exposure |
Sep 2025 | Postmark MCP supply chain | Malicious package BCC’d all processed emails to attacker server | Supply-chain compromise of MCP package | All email traffic exfiltrated |
Nov 2025 | Agent billing loop | Four AI agents entered infinite retry loop generating a $47,000 API bill in 11 days | Missing per-session cost budgets | $47,000 API billing in 11 days |
Apr 2026 | LiteLLM, LangChain, LangFlow, Flowise, Windsurf, Cursor | RCE on six live production platforms via STDIO architectural flaw (OX Advisory) | STDIO execution model plus no sanitization by default | System compromise, credential theft, supply chain event |
Gap Analysis: CSI Research Note 023 vs. Current Landscape
CSI Research Note 023 demonstrated strong foundational coverage of prompt injection, tool poisoning (TPA), supply chain risks (rug pull, typosquatting), authentication weaknesses, STDIO command injection (partially), cross-tenant data leakage (conceptually), and session management weaknesses.
Eleven material threat categories were not addressed or significantly underweighted in Research Note 023. G1: MCP-as-C2 (Swarm C2), Critical severity. G2: Parasitic Toolchain (MCP-UPD), High severity. G3: API Billing Amplification via Phantom, High severity. G4: Post-Update Privilege Persistence, High severity. G5: Full Schema Poisoning beyond description fields, High severity. G6: Advanced Tool Poisoning via response bodies bypassing static analysis, High severity. G7: Multi-Agent Delegation Edge Attacks requiring inter-agent edge instrumentation, Critical severity. G8: Persistent Memory Injection creating cross-session behavioral manipulation, High severity. G9: MCP Preference Manipulation (MPMA), Low severity. G10: SSRF Chaining to Prompt Injection (RAXE-2026-034 pattern), High severity. G11: Confused Deputy via OAuth Consent Bypass enabling one-click account takeover, Critical severity.
Three additional areas require enhancement beyond the gap list: federal and DoD-specific deployment risks with private catalog requirements and CUI boundary enforcement; developer experience as a threat vector where the protocol’s design philosophy creates security debt through developer convenience; and financial impact modeling for billing amplification and DoS via API quota exhaustion that lacks quantified risk framing in prior analysis.
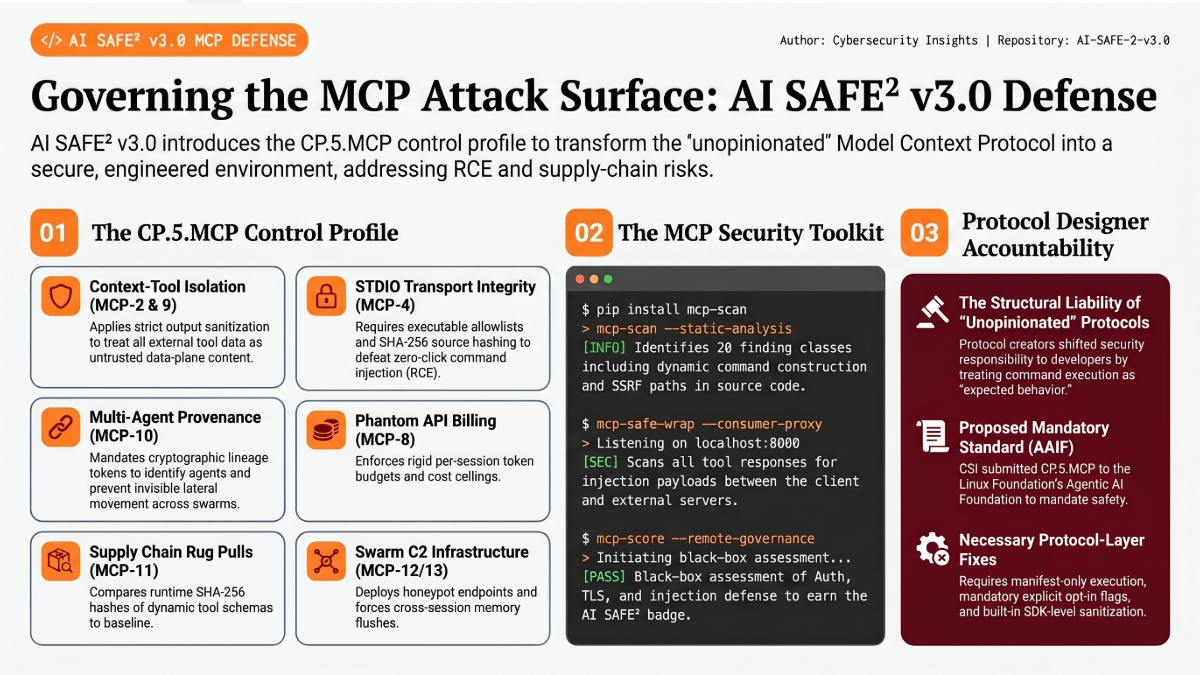
What AI SAFE2 v3.0 Provides
The AI SAFE2 v3.0 framework was not written in response to the OX disclosure. The theoretical framework for this entire threat class exists across P1.T1.10 (Indirect Injection Surface Coverage), S1.3 (Semantic Isolation Boundary Enforcement), S1.6 (Cognitive Injection Sanitization), CP.4 (Agentic Control Plane Governance), CP.5 (Platform-Specific Agent Security Profiles), and CP.7 (Deception and Active Defense Layer).
What was missing was a concrete, MCP-specific instantiation of those controls. The OX disclosure provided the empirical evidence that moved MCP from a theoretical coverage gap to a documented first-class attack surface. The result is CP.5.MCP, the MCP Server Security Profile, now a formal control in the AI SAFE2 v3.0 framework.
CP.5.MCP specifies seven required controls for MCP server operators, ACT-tier applicability, MITRE ATLAS and OWASP LLM mappings, and implementation requirements. Six additional controls (MCP-8 through MCP-13) extend the profile to cover the gap threats: billing amplification defense, context-tool isolation, multi-agent provenance and delegation edge monitoring, schema temporal profiling for rug pull classification, Swarm C2 detection via CP.7 honeypot integration, and MCP failure mode taxonomy integration with CP.1 to ensure cross-session incidents trigger full memory flush rather than session-level remediation.
Full CP.5.MCP specification: github.com/CyberStrategyInstitute/ai-safe2-framework/tree/main/00-cross-pillar
The MCP Security Toolkit
CSI has open-sourced a practical implementation of CP.5.MCP as a three-component Python package.
mcp-score runs a remote black-box CP.5.MCP assessment against any MCP HTTP server. It checks authentication posture, TLS enforcement, injection patterns across all tool descriptions and schemas, security response headers, application-layer rate limiting, session ID exposure, and SSRF surface. Builder attestation via /.well-known/mcp-security.json adds up to 25 bonus points. Servers scoring 70 or above earn the AI SAFE2 MCP badge.
mcp-scan performs static code analysis against MCP server source code across 20 finding classes covering the full CVE index from this analysis. RCE-001 through RCE-006 cover dynamic command construction, shell injection, eval, unsafe deserialization, path traversal, and kubectl argument injection. INJ-001 through INJ-005 cover output sanitization gaps, FSP surfaces, SSRF patterns, OAuth token forwarding, and rug pull exposure. Critical findings require manual review and are never auto-applied.
mcp-safe-wrap operates as a drop-in consumer-side protection layer. In STDIO mode it wraps any local server process and scans both pipe directions. In HTTP proxy mode it wraps any external HTTP MCP server, enabling organizations to route all traffic through a single scan-and-audit layer without touching any server’s code.
pip install aisafe2-mcp-tools
mcp-score https://your-mcp-server.example/mcp
mcp-scan /path/to/your/server
Source code and documentation: github.com/CyberStrategyInstitute/ai-safe2-framework/tree/main/examples/mcp-security-toolkit
Protocol Designer Accountability
The OX Security team offered Anthropic three protocol-level remediation paths before publishing. All three were declined. In a protocol with 150 million downloads and 200,000 deployment instances, that policy decision is not a security recommendation. It is a mass transfer of liability.
The parallel from web security history is instructive. Early web frameworks were also unopinionated about SQL injection. The result was a decade of breaches before prepared statements became the mandated default. The ecosystem did not fix SQL injection because developers became more careful. It fixed it because frameworks made the safe pattern the default and the unsafe pattern require explicit opt-in.
The Agentic AI Foundation under the Linux Foundation now governs the MCP specification. The governance authority to require manifest-only execution exists. The empirical evidence base for doing so is substantial: more than twenty CVEs, seven documented major incidents, and an April 2026 disclosure covering six simultaneous production compromises. CSI has submitted the CP.5.MCP control specification as a proposed standard contribution to the AAIF process.
Organizations and builders who implement CP.5.MCP now are not just protecting their current deployments. They are building the implementation expertise and governance muscle that positions them correctly for either governance scenario. The current window for being ahead of the standard rather than compliant with it is the present moment. It will not stay open indefinitely. That is the AI SAFE2 design principle applied to MCP specifically: engineered certainty at the layer you control, because you cannot wait for certainty from layers you do not control.
Frequently Asked Questions
Q1. Is the MCP STDIO vulnerability actually Anthropic’s fault?
Anthropic designed the protocol and confirmed the STDIO execution behavior as intentional. They declined three protocol-level fixes offered by OX Security before publication. The liability question is secondary to the practical question: who is responsible for fixing it at the application layer? That responsibility rests with every developer who uses the SDK.
Q2. Which platforms were actually compromised in the OX disclosure?
Six live production platforms were compromised: LiteLLM, LangChain, LangFlow (IBM), Flowise, Windsurf IDE, and Cursor. All were exploited through the same root cause inherited from the same SDK.
Q3. What does CVE-2026-30615 actually enable?
Zero-click code execution via Windsurf IDE. A malicious document or web page triggers prompt injection through the IDE’s auto-processing of repository content. The injected payload modifies the MCP configuration file. On next agent startup, the malicious STDIO entry executes. No user interaction is required after the repository is opened.
Q4. How many MCP servers are currently unprotected?
The OX Security disclosure cited 200,000 potentially vulnerable instances. Trend Micro’s July 2025 survey found 492 publicly accessible MCP servers with no authentication or encryption whatsoever. Those 492 require zero exploitation skill to access.
Q5. What is a rug pull attack and why cannot static analysis catch it?
A rug pull attack occurs when a legitimate MCP server mutates its tool descriptions after establishing user trust. The malicious payload lives in runtime metadata (the tools/list response), not in source code. Static analysis scans code at rest. The attack surface does not exist until the server is running and the schema is fetched.
Q6. What is Full Schema Poisoning and how is it different from Tool Poisoning?
Tool Poisoning (TPA) targets the description field of individual tools. Full Schema Poisoning (CyberArk, April 2026) extends the attack surface to parameter names, enum values, and response schemas. Defensive scanning focused only on description fields misses the majority of the FSP attack surface.
Q7. How does API Billing Amplification work and why do standard defenses miss it?
The Phantom attack embeds steering language in tool response bodies that causes the agent to believe the response is incomplete and re-invoke the tool. Standard defenses check inputs; this attack lives in outputs. The documented amplification factor is 658x, with a 97% miss rate from input-focused defenses. The November 2025 incident produced a $47,000 API bill in 11 days.
Q8. What is MCP-based Command-and-Control and why is it hard to detect?
Vectra AI demonstrated in February 2026 that MCP can serve as C2 infrastructure for offensive agent swarms. Standard C2 detection relies on beaconing signatures and anomalous connection patterns. MCP-based C2 traffic is semantically indistinguishable from legitimate enterprise AI tool use. Detection requires behavioral topology analysis at the inter-agent level, not per-request monitoring.
Q9. What is the difference between session-bounded and cross-session injection attacks?
Session-bounded attacks (Tool Poisoning, billing amplification) affect only the current context window. Cross-session attacks (Persistent Memory Injection, MCP-UPD) place malicious content into the agent’s persistent memory, affecting all future sessions indefinitely. The remediation is different: session attacks require session-level response to the incident. Cross-session attacks require full memory flush across all agents in the deployment.
Q10. Why did nine of eleven MCP registries accept the malicious test package?
MCP registries operate as package distribution platforms with minimal security review investment. The competitive incentive for registries is completeness and developer adoption, not security vetting. Each individual registry has limited incentive to invest in vetting infrastructure that benefits the entire ecosystem. This is a collective action problem without a voluntary solution.
Q11. What does the AI SAFE2 CP.5.MCP scoring rubric actually measure?
The 100-point rubric covers authentication posture (0-25), TLS enforcement (0-15), tool description injection patterns (0-20), Full Schema Poisoning markers (0-10), security response headers (0-10), application-layer rate limiting (0-10), session ID exposure (0-5), and SSRF surface (0-5). Builder attestation via /.well-known/mcp-security.json adds up to 25 bonus points for controls that cannot be remotely verified.
Q12. What is the HEAR Doctrine and when does it apply to MCP deployments?
The Human Ethical Agent of Record (CP.10) is a named individual with unilateral authority to stop any autonomous agent in their boundary in real time, including via cryptographic kill-switch for Class-H actions. It applies to all ACT-3 (autonomous with post-hoc review) and ACT-4 (orchestrator of other agents) deployments. MCP-connected agents at these tiers require a designated HEAR.
Q13. What is the governance trajectory for the MCP protocol?
CSI assesses two scenarios: Scenario A (55% probability by 2028) has the AAIF mandating protocol-level fixes and the ecosystem consolidating around audited registries. Scenario B (45%) has governance moving slower than adoption, with attackers developing persistent MCP-specific toolkits. CSI has submitted CP.5.MCP as a proposed standard contribution to the AAIF process.
Q14. How does AI SAFE2 v3.0 CP.5.MCP differ from OWASP LLM guidance?
OWASP LLM Top 10 identifies vulnerability categories. CP.5.MCP provides 13 specific, implementable controls with ACT tier applicability, CVSS-level severity assignments, fix templates, and a scoring rubric with a badge system. CP.5.MCP is engineered for enforcement, not awareness.
Q15. What is the minimum viable protection for an enterprise using MCP today?
Three immediate actions: audit all MCP configuration files and remove unverified servers; rotate all credentials that MCP-connected agents could have accessed since January 2026; run mcp-score against every external server before trusting it with production access. Servers scoring below 50 should not touch production systems.
Q16. Does mcp-safe-wrap protect against all MCP threat classes?
No. mcp-safe-wrap provides runtime injection scanning and SSRF blocking. It addresses MCP-2 and MCP-6 controls. It does not prevent STDIO command injection in the underlying server (mcp-scan identifies that). It does not prevent rug pull attacks beyond single-session detection. It is defense-in-depth, not a complete replacement for secure server implementation.
Q17. Where can security teams get the full CP.5.MCP specification and toolkit?
The complete CP.5.MCP specification including MCP-8 through MCP-13 is at github.com/CyberStrategyInstitute/ai-safe2-framework/tree/main/00-cross-pillar. The open-source toolkit (mcp-score, mcp-scan, mcp-safe-wrap) is at github.com/CyberStrategyInstitute/ai-safe2-framework/tree/main/examples/mcp-security-toolkit. Pro tokens and AI SAFE2 framework access: cyberstrategyinstitute.com/ai-safe2/