OpenClaw 2026.3.23 to 4.12 Security Upgrades
From Deep OS Containment to Privilege Escalation Defense – Analyzed Against AI SAFE²
AI SAFE² SECURITY ANALYSIS
OpenClaw Security Upgrades 2026.3.23-4.12
Series: OpenClaw Security Upgrades – Ongoing Analysis (Part 10)
Releases Covered: 2026.3.23 through 2026.4.12 (including 3.31, 4.9)
Phase 10: The Silent Failure Problem
OpenClaw Security Upgrades 2026.3.23-4.12 represent the longest and most technically dense security block in the project’s history. Dozens of patches across privilege containment, workspace integrity, ecosystem authorization, and cross-component trust. The development team has shifted from defending individual boundaries to systematically distrusting its own components, isolating nodes, sandboxes, browsers, and plugins so that compromise in one sub-system cannot inherit the admin or owner scopes of another.
Where the 3.22 and 3.23 releases defended the operating system from being exploited through the agent, the 3.23 through 4.12 block confronts a subtler problem: privilege pivoting across components that trust each other. Attackers are no longer just trying to break out of the sandbox. They are using a browser redirect to bypass SSRF filters. They are passing GIT_EXEC_PATH or KUBECONFIG environment variables to hijack an approved shell command. They are using remote node execution events to inject trusted System: prompt commands into the main agent.
This installment also confronts a specific incident that illustrates the deepest failure mode of internal governance: Bug #11766. OpenClaw was documented to let the model decide what to do if the HEARTBEAT.md file was missing. Instead, it silently auto-created an empty file that disabled the heartbeat completely. Critical background monitoring and scheduled cron jobs failed silently without alerting the operator. The dashboard stayed green. The agent was dead.
“A green dashboard is not a healthy system. It is the absence of a signal.”
Bug #11766 is the perfect illustration of why internal, app-level governance is structurally insufficient. The agent was trusted to enforce its own safety policy. The agent’s failure mode was to generate a file that neutralized the policy. Nothing external detected the failure because nothing external existed to detect it. This is the architectural pattern that every release in this series has documented: when the watcher and the watched are the same process, silent failure is the default.
This analysis evaluates the specific security improvements across this release block, extends the maturity model to its tenth phase, addresses the Bug #11766 question directly, and specifies how the AI SAFE² Control Gateway’s dynamic risk scoring, immutable audit logging, and governance-of-governance controls close the silent-failure gap that internal patching cannot.
Security Hardening Evaluation: What 3.23 Through 4.12 Actually Fix
These releases (OpenClaw Security Upgrades 2026.3.23-4.12) deploy dozens of coordinated patches across four primary defense layers. The unifying theme: OpenClaw is systematically distrusting its own internal components to prevent privilege pivoting across them.
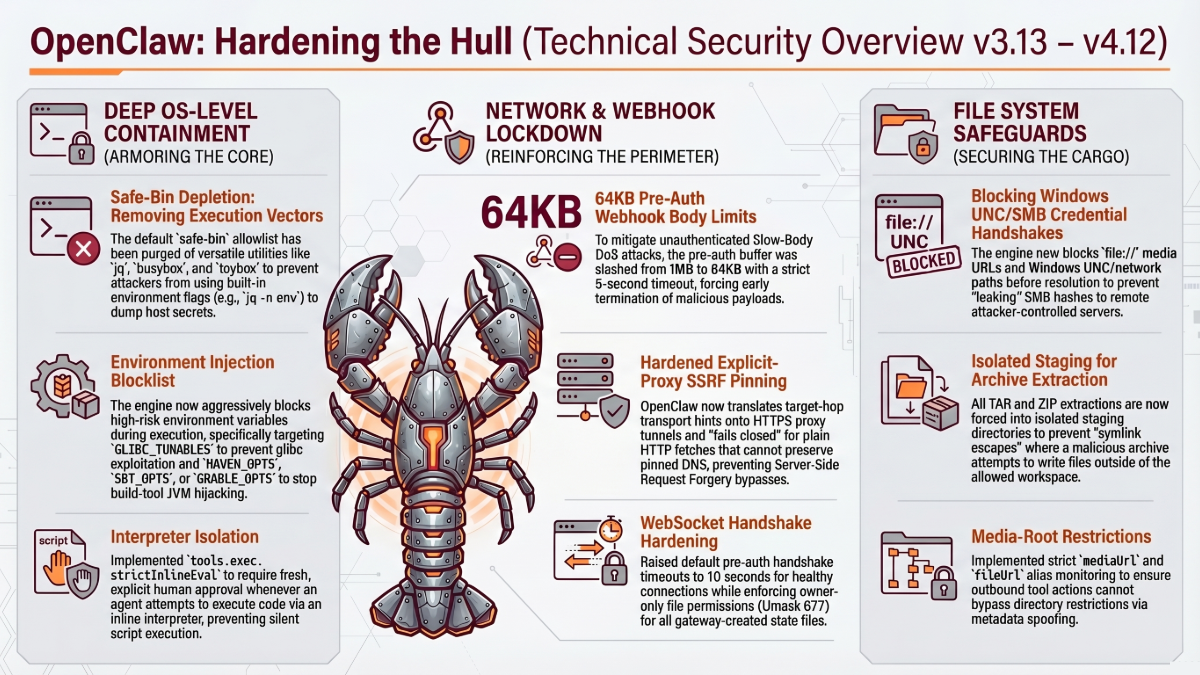
A. OepnClaw Execution and Environment Constraints
- Host Environment Sanitization: Dangerous environment overrides are blocked from being injected into host execution. This is a massive expansion covering HTTP/HTTPS proxies, TLS configuration, Docker endpoints (DOCKER_HOST), Python package indices (PIP_INDEX_URL), Java (MAVEN_OPTS), Rust/Cargo (CARGO_HOME), Git (GIT_EXEC_PATH), Kubernetes (KUBECONFIG), and cloud credential variables (AWS_*, AZURE_*, GCLOUD_*). Any of these, if attacker-controlled, can hijack a legitimate approved command to execute attacker code.
- Shell Wrapper Defenses: Shell-wrapper detection is broadened to block env-argv assignment injections (VAR=value command patterns that smuggle variables past the allowlist). busybox and toybox are removed from the interpreter-like safe binaries list because both can invoke arbitrary sub-commands internally, creating allowlist bypass vectors.
- Execution Binding: Approval-backed commands fail closed when the agent cannot bind exactly one concrete local file operand. Allow-always trust is made durable for exact-commands, preventing an approved command from silently being re-evaluated with different context later.
- Approval Failsafes: Empty approver lists no longer accidentally grant explicit authorization (a classic fail-open bug where zero approvers was interpreted as zero objections). Dangerous-tool overrides are replaced with semantic approval classes for control-plane tools, moving from per-command overrides to category-based authorization.
B. Security Hardening – Sandbox and Workspace Integrity
- Archive Traversal: TAR/ZIP extraction is hardened against destination symlinks and pre-existing child-symlink escapes. Extraction now forces files into a staging area with atomic re-opens, preventing symlink races during extraction.
- Workspace .env Limits: Untrusted workspace .env files are blocked from overriding critical runtime controls including OPENCLAW_PINNED_PYTHON and browser-control specifiers. A malicious repository with a crafted .env file can no longer silently redirect which Python binary executes.
- Media and Browser Escapes: The mediaUrl/fileUrl alias bypass is closed to enforce media-root restrictions. Persistent browser profile create, reset, and delete mutations are blocked from unauthorized node invokes, preventing cross-node profile manipulation.
C. OpenClaw Security – Network and SSRF Defenses
- Redirect Abuse: Blocked-destination safety checks now re-run after interaction-driven main-frame browser navigations, catching redirects that previously bypassed SSRF filters. Request bodies and headers are dropped on cross-origin redirects, preventing attackers from pivoting sensitive payloads across origins.
- Strict SSRF: Browser and sandbox navigation defenses are tightened against strict SSRF defaults. Trusted env-proxy setups are allowed to safely skip DNS pinning where appropriate, balancing security with legitimate proxy deployments.
- basic-ftp CRLF Injection (4.9): Command injection via CRLF sequences in basic-ftp is patched. Without this fix, attacker-controlled filenames could inject additional FTP commands into the session, enabling arbitrary file operations beyond the intended scope.
D. Identity, Gateway, and Privilege Management Workflow
- Token Revocation: WebSocket sessions and active device sessions are invalidated immediately when the shared token or password rotates. Previously, rotated tokens could leave existing sessions authenticated indefinitely.
- Strict Routing: Explicit gateway authentication is required for overlapping HTTP routes. Plugin-auth runtime clients are scoped to read-only. Owner-only tools are blocked from HTTP invoke paths, preventing web-exposed endpoints from triggering privileged operations.
- Event Trust: Remote node execution events (exec.started, exec.finished) are now marked as untrusted system events. Their outputs are sanitized so the agent cannot use remote node text to inject trusted System: prompt commands into its own context. This closes a privilege-pivoting path where a compromised remote node could influence the main agent’s behavior by crafting its output.
- Skills Path Security (4.9): A new resolveContainedSkillPath() check runs realpath() on each skill directory. Skills whose resolved paths fall outside the skills root are skipped, preventing symlink-based skill escape.
Trajectory Analysis: Ten Phases of OpenClaw Security Maturity (Release Notes)
Releases 3.23 through 4.12 establish the tenth phase: Privilege Escalation and Cross-Component Defense. The focus has shifted from defending the agent from the outside world to defending the agent’s components from each other.
Phase | Releases | Focus | Philosophy |
1 | 2026.1.29–2.1 | TLS 1.3; auth cleanup; exposure warnings | User awareness. |
2 | 2026.2.13 | SSRF, traversal, log poisoning; cred permissions | Code-level fixes. |
3 | 2026.2.19 | Auto-generated tokens; audit flags; skill doc sanitization | Secure defaults. |
4 | 2026.2.21–2.24 | Sandbox; prototype pollution; anti-evasion | Exploit containment. |
5 | 2026.2.25–2.26 | Immutable exec plans; secrets workflow; device pinning | Deep boundary enforcement. |
6 | 2026.3.1–3.7 | SecretRef 64 targets; plugin auth; hook policies | Ecosystem hardening. |
7 | 2026.3.12–3.13 | Unicode spoofing; wrapper smuggling; WebSocket hijacking | Semantic gap triage. |
8 | 2026.3.22–3.23 | GLIBC_TUNABLES; SMB/UNC blocking; JVM injection | Deep OS containment. |
9 | 2026.3.23–4.12 | Host env sanitization; workspace .env limits; event trust; token revocation; skills path realpath; CRLF injection patches | Privilege escalation defense. Components distrusting each other. |
The trajectory: Phases 1 through 8 hardened the agent against external threats: code bugs, misconfigurations, evasion techniques, parser gaps, OS-level exploits. Phase 9 inverts the problem. The threat is no longer primarily external. It is the internal trust relationships between the agent’s own components: sandboxes that trust the main gateway, plugins that trust the runtime, remote nodes that trust local nodes, browsers that trust the session context. Each trust relationship is a privilege-pivoting vector.
This is the natural maturation of a platform that has grown from a single-process agent into a multi-agent orchestration system. The security model must now reason not just about who can access what, but about how authority flows between components that were originally designed to cooperate.
“You cannot patch your way to governance.”
The Bug #11766 Problem: Why Silent Failure Is the Deepest Failure Mode
Before evaluating the AI SAFE² architecture against this release block, this installment must address an incident that illustrates the specific limitation of internal governance: OpenClaw Bug #11766.
The behavior was documented: if HEARTBEAT.md is missing, let the model decide what to do. The actual implementation: silently auto-create an empty file that disabled the heartbeat completely. Critical background monitoring stopped. Scheduled cron jobs stopped firing. The dashboard showed green. No alerts. No errors. The agent was effectively dead while appearing healthy.
This is not a corner case. It is the signature failure mode of internal, self-referential governance:
- The agent is trusted to enforce its own safety policy.
- The agent’s failure mode is to generate a file that neutralizes the policy.
- Nothing external detects the failure because the governance and the governed are the same process.
- The absence of alerts is interpreted as the presence of safety.
“When the watcher and the watched are the same process, silent failure is the default, not the exception.”
Bug #11766 demonstrates exactly why AI SAFE²’s external architecture exists. The Control Gateway, the Scanner, and the Ghost File protocol operate in different processes, on different machines, under different authentication. They cannot be silently neutralized by the agent they monitor. They generate positive signals, not just absence of alerts.
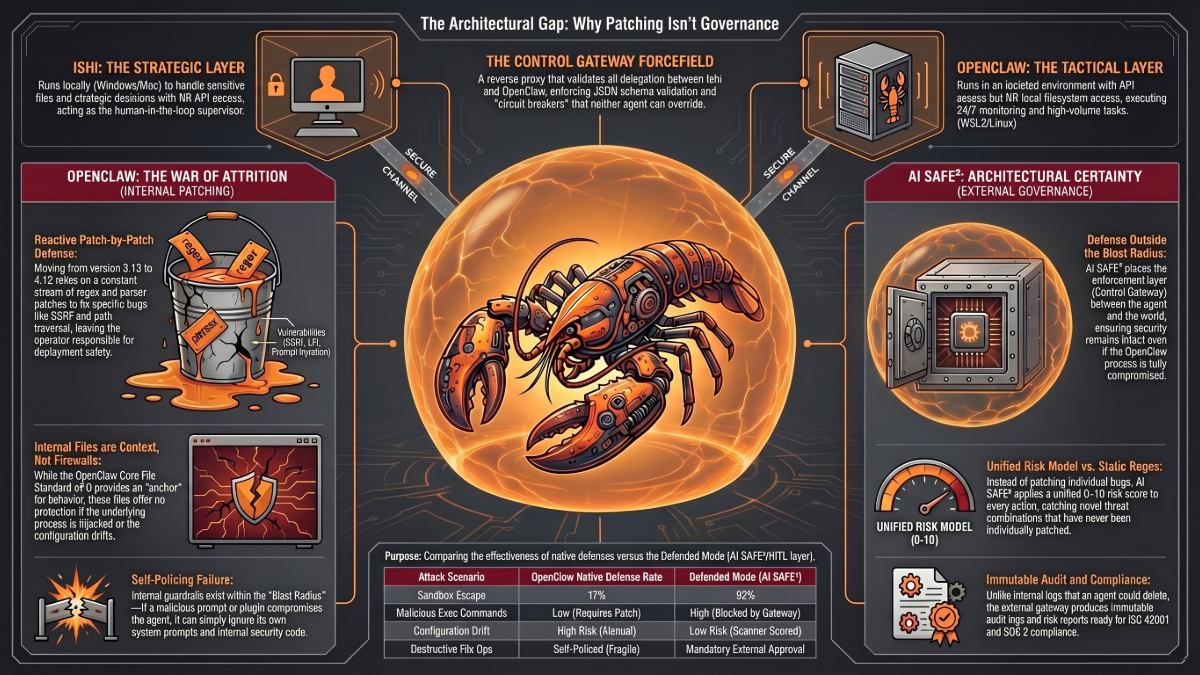
AI SAFE² Architecture: External Enforcement Against Silent Failure
The AI SAFE² Framework contains both internal hygiene components (the Core File Standard v2.0) and external architectural components. The internal components are valuable but not security boundaries. The external components are what break the attrition cycle and, critically, what catch silent failures like Bug #11766. This section specifies how each external layer operates.
A. The Control Gateway: Dynamic Risk Scoring, Not Static Allowlists
OpenClaw (3.23 to 4.12): Blocks dozens of environment variables from host execution. Removes busybox and toybox from safe-bins. Patches basic-ftp CRLF injection. Each fix extends the internal allowlist or blocklist by one entry. The adversary’s creativity outpaces the list.
AI SAFE² Control Gateway: Does not rely on a static list of bad commands. Uses a dynamic, context-aware risk scoring algorithm (0-10) with deterministic rules whose resulting score adjusts across three vectors:
- Action Type: read = 0, write = 5, delete = 10.
- Target Sensitivity: public files = 0, personal files = 5, system files = 10.
- Historical Context: frequent action = 0, rare action = 5, never-before-seen = 10.
The operator specifies threshold limits in the Gateway configuration (default: block at score 8+). Crossing thresholds does not trigger silent failure. It triggers context-dependent Human-in-the-Loop circuit breakers:
- Low-risk actions are logged and auto-approved.
- Medium-risk actions require simple approval.
- High-risk actions require explicit confirmation with a written reason.
- Critical actions (financial transactions, bulk deletions) trigger out-of-band 2FA verification.
The Difference: OpenClaw catalogs dangerous syntax. The Gateway scores dangerous outcomes. A novel shell wrapper that bypasses every syntax filter still produces a destructive outcome that the risk model classifies. One defense grows by enumeration. The other grows by observation.
“Detection is a strategy of hope. Certainty is a strategy of engineering.”
B. Immutable Audit Logging: The Circuit Breaker That Audits Itself
Every time the Gateway evaluates an action, it generates a cryptographically secure log entry including: exact timestamp, the file modified, the calculated risk score (e.g., 1.5), the tokens used, and whether the user approved it. Because this log is generated at the API-gateway layer, physically outside OpenClaw’s own process, a compromised agent cannot tamper with the evidence.
This directly addresses the Bug #11766 failure mode. If OpenClaw had been wrapped in the Control Gateway, the heartbeat disable event would have generated a positive audit entry. The absence of subsequent cron executions would have been detectable as a pattern change in the immutable log. The silent failure would have surfaced.
C. Governance of the Governor: Preventing Circuit Breaker Drift
A legitimate question arises: if the Control Gateway is the external governor, what governs the governor? What prevents the Gateway itself from drifting or failing silently like OpenClaw’s HEARTBEAT.md? AI SAFE² answers this through the Evolve & Educate pillar, which mandates physical auditing of the defense matrix through three codified mechanisms:
- Quarterly Red-Team Drills: Operators run scheduled adversarial exercises in an isolated environment, actively attempting to bypass the Gateway using prompt injection, sandbox escapes, and context overflows. Success or failure is documented. Drift is detected through comparison to prior drill baselines.
- Semi-Annual A2A Impersonation Tests: Specific drills verify the Gateway correctly catches malicious agent-to-agent orchestration. As OpenClaw has grown into multi-agent platforms, A2A attacks become a primary vector for privilege pivoting between components.
- Vulnerability Scanner (scanner.py): An external script runs nightly to audit the host’s configuration state: secret sprawl, network exposure, disabled logging, world-writable data directories, exposed gateway bindings. The Scanner runs outside OpenClaw and outside the Gateway, providing independent signal.
Ultimately, the governor is governed by architectural separation of concerns. OpenClaw acts as the tactical execution engine. The Control Gateway sits externally as the strategic governance layer. If OpenClaw fails silently (as in Bug #11766), the Gateway’s immutable logs and active Scanner provide the independent visibility needed to catch it. If the Gateway fails, the Scanner and red-team drills catch the drift. Each layer watches a different layer. No single component can silently neutralize the system.
“Never build an engine you cannot kill. And never build a governor you cannot audit.”
D. The Command Center: Isolation by Physics
OpenClaw (3.23 to 4.12): Internal UID permission narrowing and configuration settings keep the agent from accessing files it shouldn’t. Sandbox session-tree visibility is enforced. Remote node events are marked untrusted. Each fix narrows the trust between components within the same monolithic runtime.
AI SAFE² Command Center: Physically separates the Strategic Layer (Ishi, running locally with sensitive file access, no internet API credentials) from the Tactical Layer (OpenClaw, running remotely with internet and API access, no local files). A poisoned prompt injected via web search into OpenClaw cannot exfiltrate your local investor emails because the web-facing agent is physically air-gapped from your local filesystem.
The Difference: OpenClaw narrows internal trust relationships through configuration. The Command Center eliminates the trust relationship through physical separation. Configuration can drift. Physics cannot.
“Hygiene is not a firewall. Files inside the cage cannot protect against the cage being opened.”
E. Ghost Files: Business Logic, Not Syntax
OpenClaw (3.23 to 4.12): Removes busybox from safe-bins. Strips single-quoted $0 tokens from shell wrappers. Blocks env-argv assignment injections. Each fix extends the syntax-parsing game.
AI SAFE² Ghost Files: Pause high-risk actions based on business impact rather than syntax. If the agent attempts to delete a database, move sensitive files, or transfer funds, the action is paused for Human-in-the-Loop approval regardless of how the command was constructed. Syntax obfuscation is rendered irrelevant because the defense operates on outcomes.
Control Mapping: OpenClaw 2026.3.23 to 4.12 vs. AI SAFE²
Security Domain | OpenClaw 3.23-4.12 (Native) | AI SAFE² (External Enforcement) |
Environment Integrity | Host env sanitization (HTTP proxies, TLS, Docker, PIP, MAVEN, Cargo, Git, KUBECONFIG, cloud creds). Workspace .env override limits. | Control Gateway enforces egress policy independent of agent’s internal env handling. Scanner detects env drift nightly. |
Execution / Approval | Empty approver list fail-closed. Allow-always durable for exact commands. Semantic approval classes for control-plane tools. | Ghost Files pause destructive actions for HITL review. Dynamic risk scoring (0-10) across action type, target sensitivity, historical context. |
Component Trust | Remote node events marked untrusted. Sandbox session-tree visibility. Plugin runtime clients read-only. Owner tools blocked from HTTP. | Command Center: Ishi (local/private) physically separated from OpenClaw (remote/tactical). Cross-component compromise contained by architecture. |
Network / SSRF | Redirect re-checks after browser navigation. Cross-origin body/header stripping. basic-ftp CRLF patch. Strict SSRF with env-proxy exceptions. | Control Gateway as external reverse proxy enforces PII blocking, JSON schema validation, Circuit Breakers. Independent of agent’s internal network code. |
Silent Failure Detection | N/A. Bug #11766 demonstrates OpenClaw cannot detect its own silent failures. The agent and the watcher are the same process. | Immutable Audit Log + nightly Scanner + quarterly red-team drills + semi-annual A2A impersonation tests. Pattern changes surface silently-disabled controls. |
Governance of Governance | N/A. | Evolve & Educate pillar: architectural separation of concerns. Each layer audits a different layer. No single component can silently neutralize the system. |
Compliance | Audit tool findings. No ISO 42001 / SOC 2 evidence. | Unified Audit Log: cryptographically signed, risk-scored, ISO 42001 / SOC 2 mapped. SIEM integration. |
The Verdict: Architecture Over Attrition, Signal Over Silence
OpenClaw releases 3.23 through 4.12 represent extraordinary engineering. Systematic distrust of internal components. Environment sanitization across a dozen runtime ecosystems. Privilege pivoting closed across browser, sandbox, plugin, and node boundaries. The velocity and technical depth is unmatched.
It is also a war of attrition that grows faster than any patching cadence can sustain. Each release closes specific privilege-pivoting paths. Each new runtime integration, each new environment variable, each new wrapper script opens new ones. The defender must enumerate all paths. The attacker needs one.
Bug #11766 is the structural illustration: when the agent governs itself, silent failure is inevitable. Not possible. Inevitable. The absence of alerts becomes the evidence of safety, and the absence of alerts is exactly what silent failure produces.
“You cannot audit a millisecond with a weekly meeting. You cannot detect a silent failure with the process that is failing silently.”
The standard: AI SAFE²’s Core File Standard v2.0 is valuable internal hygiene. It is not a security boundary. The components that break the attrition cycle and catch silent failures are external and physical: the Control Gateway (dynamic risk scoring, immutable logging), the Command Center Architecture (physical isolation), Ghost Files (outcome governance), and the Scanner (independent nightly auditing). Deploy those. The internal files are a bonus. The external architecture is the requirement.
“Policy is just intent. Engineering is reality.”
Recommended Action
Immediate: Apply OpenClaw 3.23 through 4.12. Priority fixes include host environment sanitization (GIT_EXEC_PATH, KUBECONFIG, cloud creds), remote node event trust marking, and the basic-ftp CRLF patch in 4.9. Verify busybox and toybox are removed from your safe-bin allowlist. Test workspace .env override handling against your repository topology.
Next: Run the AI SAFE² Scanner to detect silent-failure patterns in your deployment (disabled logging, missing heartbeat files, drifted configurations). Check for any HEARTBEAT.md files that may have been silently auto-created in the Bug #11766 pattern.
Strategic: Deploy the AI SAFE² Control Gateway with risk-scoring thresholds appropriate to your risk tolerance (default: block at 8+). Configure Immutable Audit Logging with SIEM integration. Schedule quarterly red-team drills and semi-annual A2A impersonation tests. Deploy the Command Center Architecture for physical isolation of sensitive data from the tactical agent. The goal is not to trust OpenClaw. The goal is to make OpenClaw’s trustworthiness irrelevant to your security posture.
“Milliseconds beat committees. Architecture beats attrition.”
Download the AI SAFE² Toolkit for OpenClaw
Schedule a Threat Exposure Assessment
Previous in Series: 3.22-3.23 | 3.12-3.13 | 3.1-3.7 | 2.13 | 1.29 & 2.1
FAQ: OpenClaw 2026.3.23 to 2026.4.12 Security Upgrades and AI SAFE² Governance
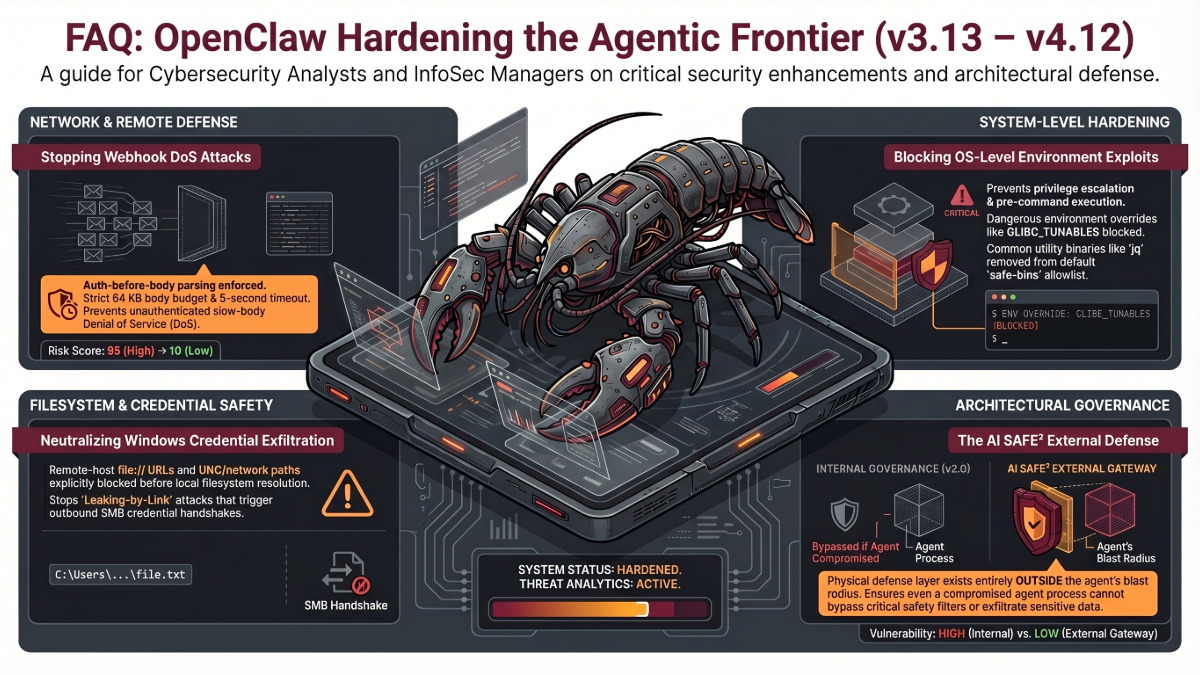
17 questions practitioners are asking about this release block, Bug #11766, and the AI SAFE² governance architecture.
1. Why cover so many releases (3.23 through 4.12) in a single article?
This block represents a unified theme: privilege escalation and cross-component defense. Across roughly three weeks of releases, OpenClaw systematically distrusted its own internal components – sandboxes, plugins, remote nodes, browsers, and workspaces. Covering them together reveals the coherent defensive posture: the agent is no longer just defending against external attackers; it is defending against privilege pivoting between components that previously trusted each other.
2. What is Bug #11766 and why is it important?
OpenClaw was documented to let the model decide what to do if the HEARTBEAT.md file was missing. Instead, it silently auto-created an empty file that disabled the heartbeat completely. Critical background monitoring and scheduled cron jobs failed silently. No alerts. No errors. The dashboard stayed green. The agent was effectively dead while appearing healthy. This is the signature failure mode of internal self-governance: when the watcher and the watched are the same process, silent failure is the default.
3. How does AI SAFE²’s Control Gateway specify its deviation threshold?
The Gateway does not rely on a static list of bad commands. It uses a dynamic, context-aware risk scoring algorithm (0-10) with deterministic rules whose resulting score adjusts across three vectors: Action Type (read=0, write=5, delete=10), Target Sensitivity (public=0, personal=5, system=10), and Historical Context (frequent=0, rare=5, never-before-seen=10). The operator specifies threshold limits in Gateway configuration, defaulting to block at score 8 or higher.
4. What happens when an action crosses the risk threshold?
Rather than causing a silent failure, crossing thresholds triggers context-dependent Human-in-the-Loop circuit breakers. Low-risk actions are logged and auto-approved. Medium-risk actions require simple approval. High-risk actions require explicit confirmation with a written reason. Critical actions like financial transactions or bulk deletions trigger out-of-band 2FA verification. The response scales to the risk.
5. Who audits the circuit breaker itself?
The circuit breaker audits itself through Immutable Audit Logging. Every time the Gateway evaluates an action, it generates a cryptographically secure log entry detailing exact timestamp, file modified, calculated risk score (e.g., 1.5), tokens used, and whether the user approved. Because this log is generated at the API-gateway layer physically outside OpenClaw’s own process, a compromised agent cannot tamper with the evidence.
6. Who governs the governor? What prevents the Gateway from failing silently like Bug #11766?
AI SAFE² enforces the Evolve & Educate pillar, which mandates physical auditing of the defense matrix. This is codified through three mechanisms: Quarterly Red-Team Drills (operators run scheduled adversarial exercises attempting to bypass the Gateway using prompt injection, sandbox escapes, and context overflows), Semi-Annual A2A Impersonation Tests (drills to verify the Gateway catches malicious agent-to-agent orchestration), and the Vulnerability Scanner (scanner.py) which runs nightly to audit host configuration state for secret sprawl, network exposure, and disabled logging. Ultimately, the governor is governed by architectural separation of concerns: OpenClaw is the tactical execution engine; the Gateway is the strategic governance layer. Each layer audits a different layer.
7. What environment variables did 3.23 through 4.12 block, and why do they matter?
The block list expanded significantly to cover HTTP/HTTPS proxies, TLS configuration, Docker endpoints (DOCKER_HOST), Python package indices (PIP_INDEX_URL), Java (MAVEN_OPTS, SBT_OPTS, GRADLE_OPTS), Rust/Cargo, Git (GIT_EXEC_PATH), Kubernetes (KUBECONFIG), and cloud credentials (AWS_*, AZURE_*, GCLOUD_*). Any of these, if attacker-controlled in the agent’s execution environment, can hijack a legitimate approved command to execute attacker code. GIT_EXEC_PATH alone redirects where git looks for its subcommands, letting an attacker replace git commit with arbitrary code.
8. Why were busybox and toybox removed from the safe-bin list?
Both busybox and toybox are multi-call binaries: they contain dozens of built-in sub-commands invoked through symlinks or the first argument. If either is on the safe-bin allowlist, an attacker can invoke any internal command (sh, wget, nc, etc.) through the allowed binary, completely bypassing the intent of the allowlist. Removing them eliminates this class of allowlist bypass.
9. What is the remote node event trust fix and what privilege-pivoting did it prevent?
Previously, remote node execution events (exec.started, exec.finished) were processed as trusted system events. Their outputs could contain text that the main agent interpreted as System: prompt commands, effectively allowing a compromised remote node to inject instructions into the main agent’s context. The fix marks these events as untrusted and sanitizes their outputs before they reach the agent’s prompt. This closes a cross-component privilege escalation path where compromising a remote node could lead to compromising the main agent.
10. What is the workspace .env override limit?
An untrusted workspace (for example, a cloned malicious repository) could previously include a .env file that overrode critical runtime controls like OPENCLAW_PINNED_PYTHON or browser-control specifiers. This meant checking out an attacker-controlled repository could silently redirect which Python binary executed or change browser security policies. The fix blocks workspace .env files from overriding these specific control variables, keeping critical runtime settings under operator control rather than repository control.
11. How does the basic-ftp CRLF injection patch work (4.9)?
basic-ftp is a common Node.js FTP client dependency. Without validation, attacker-controlled filenames could contain CRLF (\r\n) sequences that inject additional FTP commands into the session. A file operation that appears to fetch one file could execute multiple FTP commands, potentially including directory deletion, permission changes, or arbitrary file uploads. The 4.9 patch sanitizes filenames to reject CRLF sequences before they reach the FTP command stream.
12. What are the ten phases of OpenClaw’s security maturity?
Phase 1: User awareness. Phase 2: Code-level fixes. Phase 3: Secure defaults. Phase 4: Exploit containment. Phase 5: Deep boundary enforcement. Phase 6: Ecosystem hardening. Phase 7: Semantic gap triage. Phase 8: Deep OS containment. Phase 9: Privilege escalation and cross-component defense. Each phase addresses a higher-order threat class, and Phase 9 represents the shift from defending against external attackers to defending internal trust relationships between components.
13. Why is the Core File Standard v2.0 explicitly called ‘not a security boundary’ in this series?
The Core File Standard (SOUL.md, IDENTITY.md, TOOLS.md, HEARTBEAT.md, and related files) provides valuable cognitive hygiene for the agent. But these are text files inside the agent’s environment. If a zero-day exploit compromises the process – or if, as in Bug #11766, the agent itself silently neutralizes the file – the internal governance fails with the agent. The external components (Control Gateway, Command Center, Ghost Files, Scanner) operate in different processes on different machines under different authentication. They survive a process compromise. The internal files do not.
14. How does Immutable Audit Logging detect failures like Bug #11766?
If Bug #11766 had occurred in a deployment wrapped by the AI SAFE² Control Gateway, the heartbeat-disable event would have generated a positive audit entry. The subsequent absence of scheduled cron task executions would have produced a pattern change detectable in the immutable log. The Scanner running nightly would have flagged disabled logging or missing heartbeat signatures. The silent failure would have surfaced because external signals do not depend on the compromised agent to report them.
15. What compliance gaps remain after 3.23 to 4.12?
OpenClaw’s patches are engineering-grade vulnerability management. They do not produce compliance evidence. There is no immutable audit log with risk scores, no authorization attribution per action, no policy conformance reporting, and no SIEM integration. For organizations subject to ISO 42001, SOC 2, HIPAA, or financial regulation, the gap between privilege containment and compliance readiness is the gap between engineering confidence and legal defensibility. AI SAFE²’s Unified Audit Log with cryptographic signing bridges this gap.
16. How should I sequence 3.23 through 4.12 updates with AI SAFE² deployment?
Apply updates in order, testing workspace .env behavior and safe-bin changes in staging first. Verify your deployment does not depend on busybox or toybox in the allowlist. Check for Bug #11766 patterns: look for auto-created HEARTBEAT.md files and verify heartbeat telemetry is actually reaching your monitoring. Deploy the AI SAFE² Scanner for nightly independent auditing. Deploy the Control Gateway with risk-scoring thresholds calibrated to your risk tolerance. Configure Immutable Audit Logging with SIEM integration. Deploy the Command Center Architecture to physically isolate sensitive data from the tactical agent. Schedule the first red-team drill within 30 days of Gateway deployment.
17. What is the most important insight from 3.23 to 4.12?
Bug #11766 is the most important finding of this block, not any individual GHSA. It demonstrates that the deepest failure mode of agentic AI is not external attack but internal silent drift: the agent fails in a way that neutralizes its own safety controls while appearing healthy to itself. No amount of internal patching prevents this class of failure because the patching and the failing are the same process. The only structural defense is external governance with independent signal generation. The Control Gateway, the Scanner, the red-team drills, and the Command Center are not optional hardening. They are the architectural requirement for detecting failures that the agent itself cannot detect.