Cybersecurity in Healthcare Merger and Acquisition (M&A): Managing Risks to Ensure Successful M&A Integration and ROI
The Critical Importance of Due Diligence in Healthcare M&A: Safeguarding IT Assets and Mitigating Cybersecurity Risks As healthcare systems increasingly pursue mergers […]
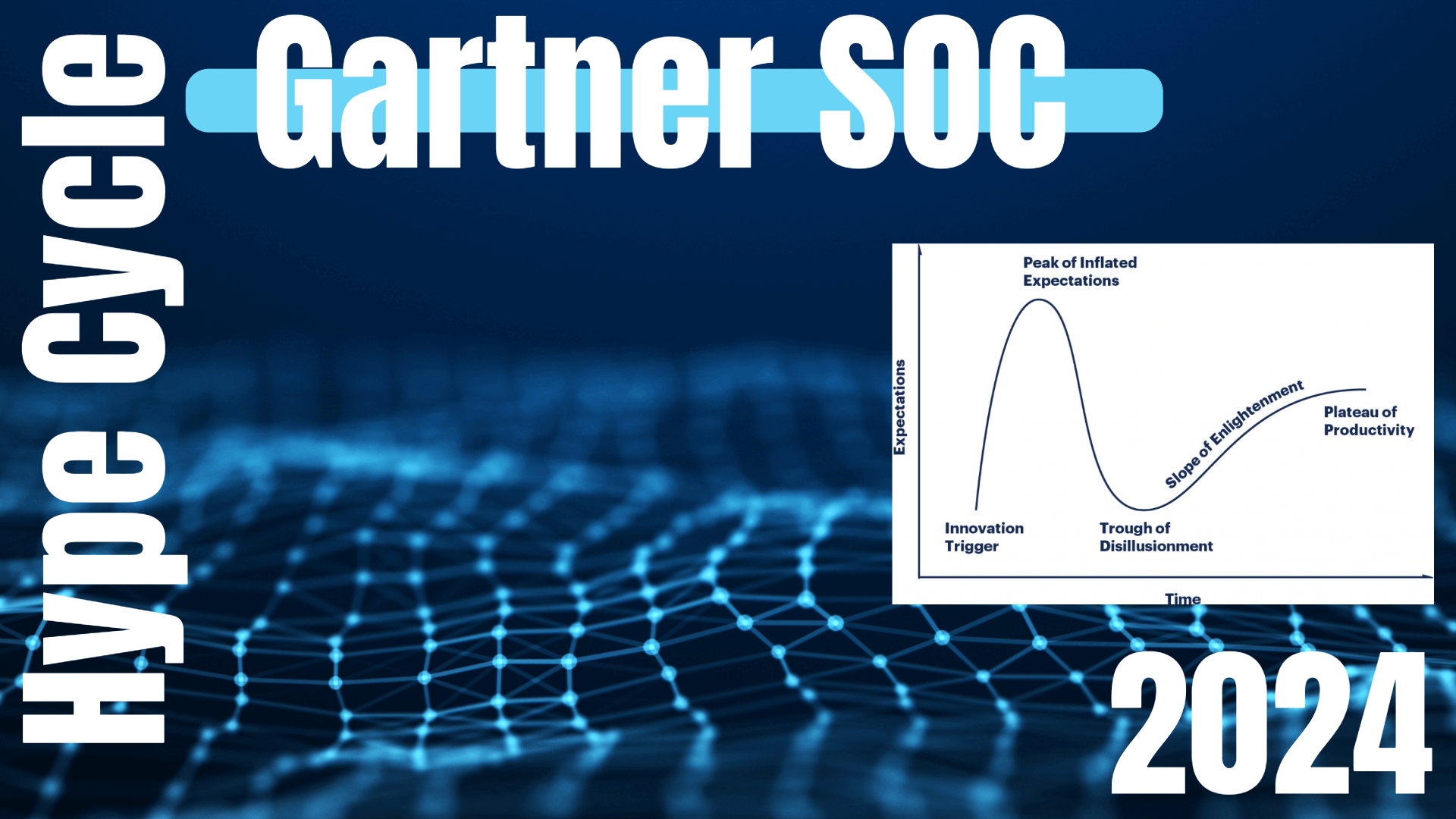
Gartner Analysis of Security Operations Centers (SOCs) in 2024 – Understanding the Hype Cycle™ for Security Operations
The Evolution of Cybersecurity Gartner Analysis of Security Operations Centers (SOCs) in 2024: New Trends, Challenges, and Innovations Gartner Analysis of Security Operations Centers […]
Microsoft States Zero Trust is the Future – Microsoft’s Endorsement is a Game Changer
Microsoft Endorsement for a Zero Trust Strategy As the digital landscape evolves, traditional security models are proving increasingly ineffective at preventing today’s […]
Navigating Zero Trust Security Solutions and Their Boundaries: Tough Questions Every Enterprise Should Ask in order to Implement Zero Trust
Key Considerations for Selecting and Avoiding Common Pitfalls in Implementing Zero Trust Security Solutions In today’s rapidly evolving cybersecurity landscape, Zero Trust […]

CISA has stated that K-12 Cybersecurity Threats are Rising – Schools have a way to onboard top Cybersecurity Solutions if they do…
Ransomware Attacks on Schools Are Escalating: How Schools Can Secure FCC Grants with a Proactive Cybersecurity Strategy Ransomware attacks on schools and […]

Why is Microsoft Allowing Hacks and the Case for Zero Trust?
Overview of Systemic Flaws Including Microsoft Security Failures and High-Profile Email Hacks Incident Summary In recent years, multiple high-profile cyberattacks have revealed […]
Ransomware on the Rise: How K-12 Schools are Becoming Prime Targets & How K-12 Cybersecurity Should Respond?
Federal and State Responses to the K-12 Cybersecurity Crisis: The Alarming Increase in Ransomware Attacks on K-12 Schools Cybersecurity in Crisis: The […]
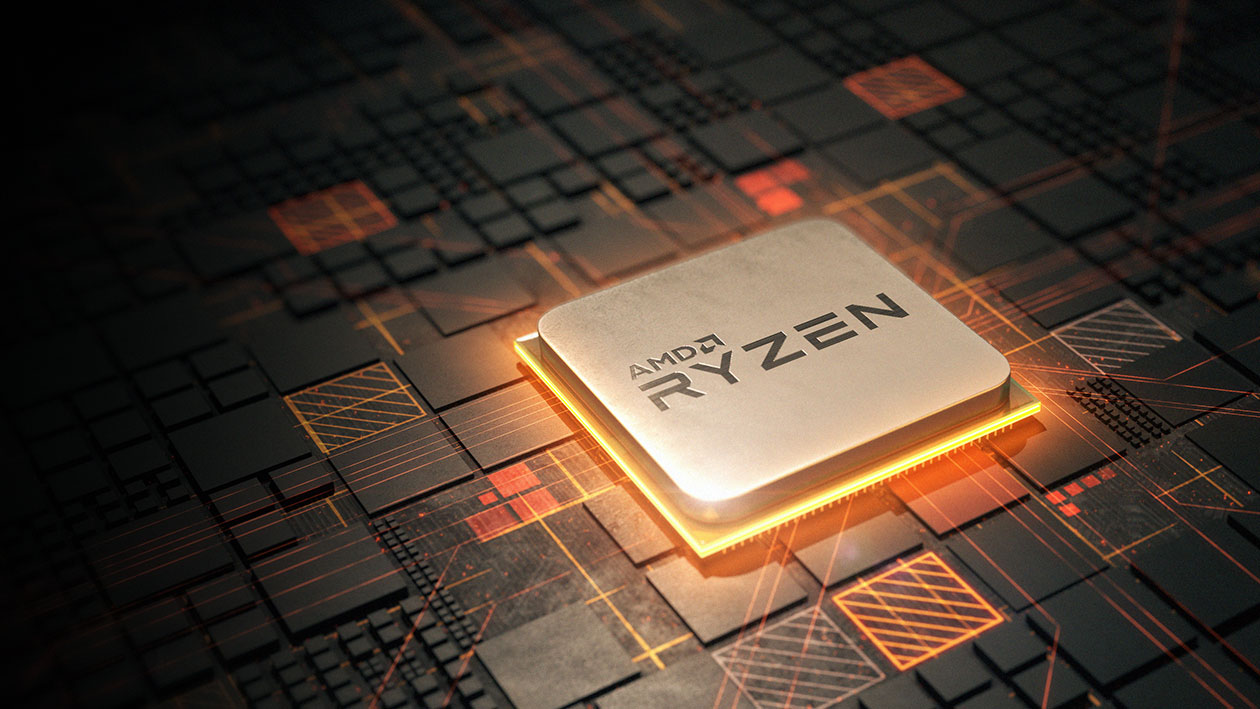
Sinkclose Vulnerability in Hundreds of Millions of AMD Chips Allows Unfixable Flaw & Possible Infections to Bootkits – Learn What to do Now!
Sinkclose Vulnerability Explained: How to Secure Your AMD Chips Flaws AMD Chip Flaw Overview of Sinkclose Security flaws within firmware, the core […]

What did Microsoft just admit about AI & AI Security out-loud? Breaking Down the Detection Flaws of the Microsoft Generative AI: The Case for Zero Trust
The Shortcomings of the Microsoft Detection-Based Cybersecurity Approach – How AI Security is Exposing the Fallacy of Detection Solutions. In an era […]

CrowdStrike Compromised: Unveiling the Hidden Threats in the Falcon CrowdStrike Outage Wake for CISOs
Architectural Flaws in CrowdStrike Caused the Outage in the CrowdStrike Update: Legal Protection for CISOs is More in Doubt Than Ever Before […]

Why Warden Zero Trust “Out-of-the-Box” Endpoint Defense Does Not Have the Same Problem as CrowdStrike Falcon
Revolutionizing Endpoint Protection: Warden Zero Trust “Out-of-the-Box” Containment vs. CrowdStrike’s Detection First Approach That Requires Frequent Kernel Updates In today’s cybersecurity landscape, […]

How Did the CrowdStrike Kernel Level Failure Impact 8.5M Microsoft Window Devices and Cause an IT Outage? – The Risks Cybersecurity Vendors Place their Clients Operations In
Crowdstrike Kernel Level Failure Just Impacted Everyday Life – 8M+ Systems in Air Travel, Banks, Emergency Services, Hospitals, and Backdoors Exploded in […]
