Federal Cybersecurity Is Losing the Race Against AI-Generated Exploits. It Needs Engineered Certainty.
Federal Cybersecurity Needs a Mindset Shift Automated Exploit Generation Changes the Future of Federal Cybersecurity The recent emergency directives from Cybersecurity and […]

2026 Shadow AI Agent & BYO-Agent Reality Report – AI Cybersecurity Threat Landscape
2026 Shadow AI & BYO-Agent Reality Report What Was Predicted in 2025. What Actually Happened. What Must Change in 2026. Purpose Statement: […]

2026 AI Cybersecurity Risks Reality Report – Cybersecurity Threat Landscape
2026 AI Cybersecurity Risks Reality Report What Was Predicted in 2025. What Actually Happened. What Must Change in 2026. Purpose Statement: This […]

2026 Supply Chain & Third-Party Risk Reality Report – Cybersecurity Threat Landscape
2026 Supply Chain & Third-Party Risk Reality Report What Was Predicted in 2025. What Actually Happened. What Must Change in 2026. Purpose […]
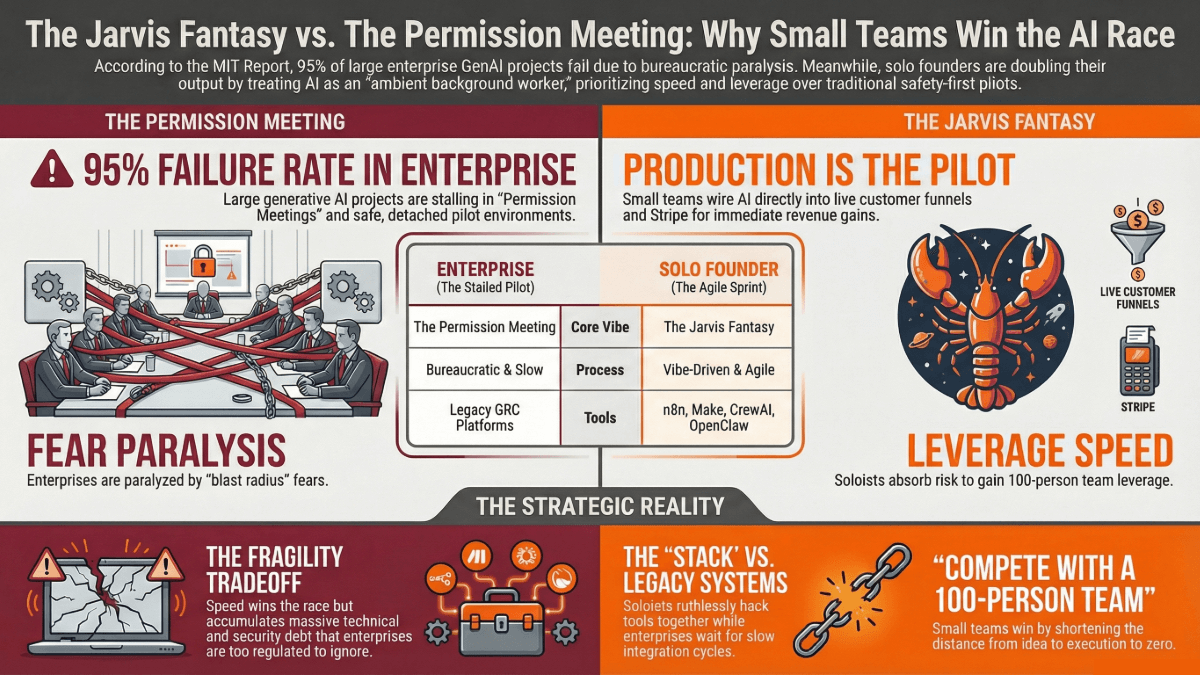
Enterprise AI Failure vs Solo Founders Generative AI Project Advantage
Enterprise AI Failure vs Solo Founders Spirit The Jarvis Fantasy vs. The Permission Meeting: Why Small Teams are Winning the Agentic AI […]

2026 Cloud Security Reality Report – Cybersecurity Threat Landscape
2025 Cloud Security Reality Report What Was Predicted in 2025. What Actually Happened. What Must Change in 2026 Purpose Statement: This report […]