Cybersecurity Corner stone
Penetration testing is one of the most reliable tools of cybersecurity to make sure that your data and your security infrastructure is consistently safe.
However, due to the iterative nature of the internet, pentesting can be similar to many other methods in the cybersecurity realm. To avoid confusion, we will explore how a pentest is different from other cybersecurity methods and tools. But first, let’s set our baseline understanding and determine what pentesting is not.
What is a Pentesting?
Penetration testing is a testing methodology that simulates a cyberattack on a system performed by ethical hackers. It has 3 different types depending on the information provided by the blue team (defenders/cybersecurity team) and provided to the red team (attackers/ethical hackers/pentesters):
- White Box — a coordinating testing between the pentesters and the security response team. Every move is telegraphed by each side. Great for training purposes and understanding how an attack works.
- Gray Box — limited information on both sides. Attackers are only minimal info, usually just the name of the target organization. Defenders are aware that a pen test will be performed, however they don’t know when or how. Closer to a real-world scenario while making sure that the blue team is still aware, so they can prepare and analyze.
- Black box — Similar to gray box, only the target name is given to the attackers. However, the defending team is not aware of the test. Only the upper management in the organization who requested the test is aware. Acts like a final exam for the defending team. Tests how the system and the blue team respond to an attack.
Now that we have a baseline knowledge of what a pen test is, let us now determine what it is not.
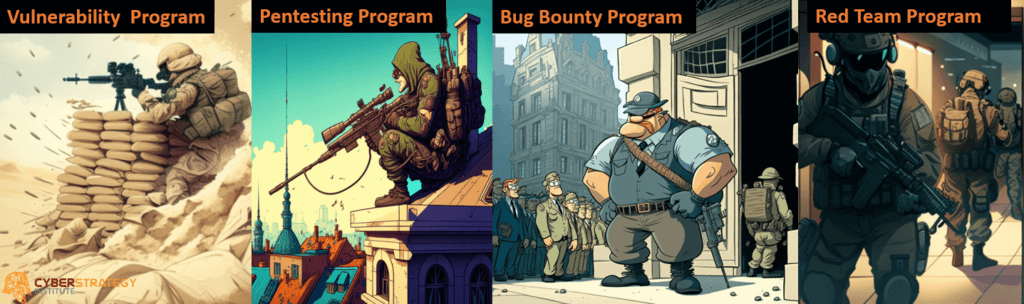
Pentesting is not a vulnerability assessment.

This term is also another semantic argument with pentesting. Technically, pentesting does aim to assess the vulnerability of a system.
However, the term “vulnerability assessment” mainly refers to unsupervised security testing that is specifically looking for vulnerabilities in software, computers or networks that are known. It has similar procedures as a pentest, but a pentest’s goals are to actually prove what is vulnerable by exploiting the system.
The main difference between a pentest and a vulnerability assessment is using a tool that produces lots of information, false positives and can mislead you on certain vulnerabilities that are actual features of your systems. Most system admins dread the results, because in some regards they have to then manual double-check everything.

While a pentest is executed by professional pentesters using known or unknown exploits in proving the systems are secure.
Other pentesting services like our Mimic system are also automated and autonomous but still bounded and observed by our testers.
Though vulnerability tests are faster and more convenient than a traditional penetration test, it can result in false positives or inaccurate recommendations. Meaning the results may not be best aligned to the business. As a result, it can be significantly less effective than a pentest and a lot more time-consuming.

The most crucial element in services like pentesting is the expertise. An IT professional with years of experience might look at a firewall and conclude that it is safe enough while a penetration tester can look closely at a firewall and truly determine if it could really function well as a defense mechanism.
But for cases in which an organization needs a quick and easy scan rather than a full-blown reconnaissance, people have an option for vulnerability testing. Sometimes, it’s already part of an antivirus package, so private individuals can also take advantage of it.
Pentesting vs Bug Bounty
Bug Bounties also have similar methodologies to a pentest; however, the delivery of the tests, the testers, and the payment system are different. Think of traditional pentesting as working with an agency while a bug bounty is working with freelancers.
A bug bounty works as it is described. An organization will contact individuals or groups of ethical hackers and then reward them when they find bugs, vulnerabilities or exploits in the system. As you can see, this might be a cost-effective way to achieve results of a pentest, while only paying for when you already have the results.
However, it’s not as thorough or as organized as a normal pentest because it’s more of an informal invitation to do a task rather than a formal contract in which proper expectations are set. This results in you never know who is actually looking at your code, system, or environment when waiting on ethical hackers to find something. They are also not responsive, meaning you are now operating on their timeline, not yours.
The reports and recommendations you’ll receive through a bug bounty may not have the same quality as a pentest. Because bug hunters are only incentivized to find weaknesses in the security controls, they may not employ a thorough testing procedure compared to a penetration test performed by organizations.
Bug hunters also don’t have the same vetting systems as the formal organizations that do official penetration tests. Bug hunters can be just budding white hat hackers, or they might actually be black hat hackers in disguise, so your information may be at risk. Another constraint is that they only provide you with enough information in order to get paid for the identified vulnerability, not what led up to it. Nor are you likely to get additional information if requested, as they don’t work for you.
So while a bug bounty might sound economical in the short-term, it has so many drawbacks that it is not really recommended by the cybersecurity community due to inconsistent results that vary overtime. It does ad-value, but if you are in a time crunch to show improvement, meet compliance requirements or recover from an incident, it will not help you get what you need.
Pentesting is not ethical hacking.
In this scenario, it’s just a semantics argument. All pen tests are ethical hacking but not all ethical hacking is a pentest.
To make it simpler, a penetration test is one of the forms of ethical hacking. Ethical hacking is not only limited to pen testing. A pentest is only one of the multiple methods that an ethical hacker can use to exploit a system and enter an application without authorization uncovering vulnerable systems, applications, networks or physical access uncovering security issues within an organization’s system.
Pentesting is not red teaming.

We know that the red team is the “attacking side” simulating advanced adversaries such as hobbyists, hackers (ethical or not), and State-Sponsored actors. Red Teams are differentiated by their objective, to exploit a flaw or combination of flaws to achieve their objective of finding or exfiltrating data.
A pentest is used to understand and uncover the security flaws and find vulnerabilities through a pre-determined simulated attack, often limited to a specific network, system or application. It’s a much more generalized and targeted test to verify the overall security status of the organization.
On the other hand, Red Teaming is a testing process performed by ethical hackers with a specific purpose: To gain access to a specific file or directory inside the system. The procedure is the same as a pentest which is to check security vulnerabilities and exploitable parts in specific parts of the security system.
Red Teaming can also be performed via a specific scenario. Where only key stakeholders in the organization are aware of the test. This is to see how the Blue Teams security measures work and show how the security team responds to a breach if detected to part of their environment. While Red Teaming is the ultimate approach, people that can effectively do Red Teams are very hard to find, hire and retain. Thus, the average organization may never get to leverage this advanced capability.
Conclusion
The reason why organizations request a penetration test is that they have traditionally been more affordable, more specific in their results, and have helped them reach compliance standards. However, myths and misperceptions around pentesting often cloud the true value these tests provide. Information is what you are paying for, even if it is not quickly turned around by the pentesters (averaging 2–6 weeks to get the final report). An organization’s goal should be to get to the point that they can test more frequently.
The ultimate objective is to run a pentest after every major change to systems, network or applications to verify that those patches worked. The challenge has been the organizational costs to schedule these events. Even if you have them internal to your organization, scheduling resources and capturing their results takes time. This is why people are moving towards Pentesting as a Service (PaaS) providers. Leveraging their platforms allows you to scale up your Pentesting from annual or 2–4 times a year, to monthly, weekly or on-demand. This is the future, leveraging Artificial Intelligence (AI) or advanced Machine Learning (ML) approaches to learn your organization’s environment and constantly be able to leverage a PaaS platform to not just trust things have been fixed, but verify they are secure!
If your interested in learning more about PaaS, checkout Mimic!