
CISA has stated that K-12 Cybersecurity Threats are Rising – Schools have a way to onboard top Cybersecurity Solutions if they do…
Ransomware Attacks on Schools Are Escalating: How Schools Can Secure FCC Grants with a Proactive Cybersecurity Strategy Ransomware attacks on schools and […]

Why is Microsoft Allowing Hacks and the Case for Zero Trust?
Overview of Systemic Flaws Including Microsoft Security Failures and High-Profile Email Hacks Incident Summary In recent years, multiple high-profile cyberattacks have revealed […]

How to Secure State and Local Cybersecurity Grants: A Step-by-Step Guide for those Wanting FCC School and Library Grant Funding
Introduction for Those Looking for State and Local Cybersecurity Grant Programs for K-12 Schools With the increasing frequency of cybersecurity threats in […]
Ransomware on the Rise: How K-12 Schools are Becoming Prime Targets & How K-12 Cybersecurity Should Respond?
Federal and State Responses to the K-12 Cybersecurity Crisis: The Alarming Increase in Ransomware Attacks on K-12 Schools Cybersecurity in Crisis: The […]
Sinkclose Vulnerability in Hundreds of Millions of AMD Chips Allows Unfixable Flaw & Possible Infections to Bootkits – Learn What to do Now!
Sinkclose Vulnerability Explained: How to Secure Your AMD Chips Flaws AMD Chip Flaw Overview of Sinkclose Security flaws within firmware, the core […]
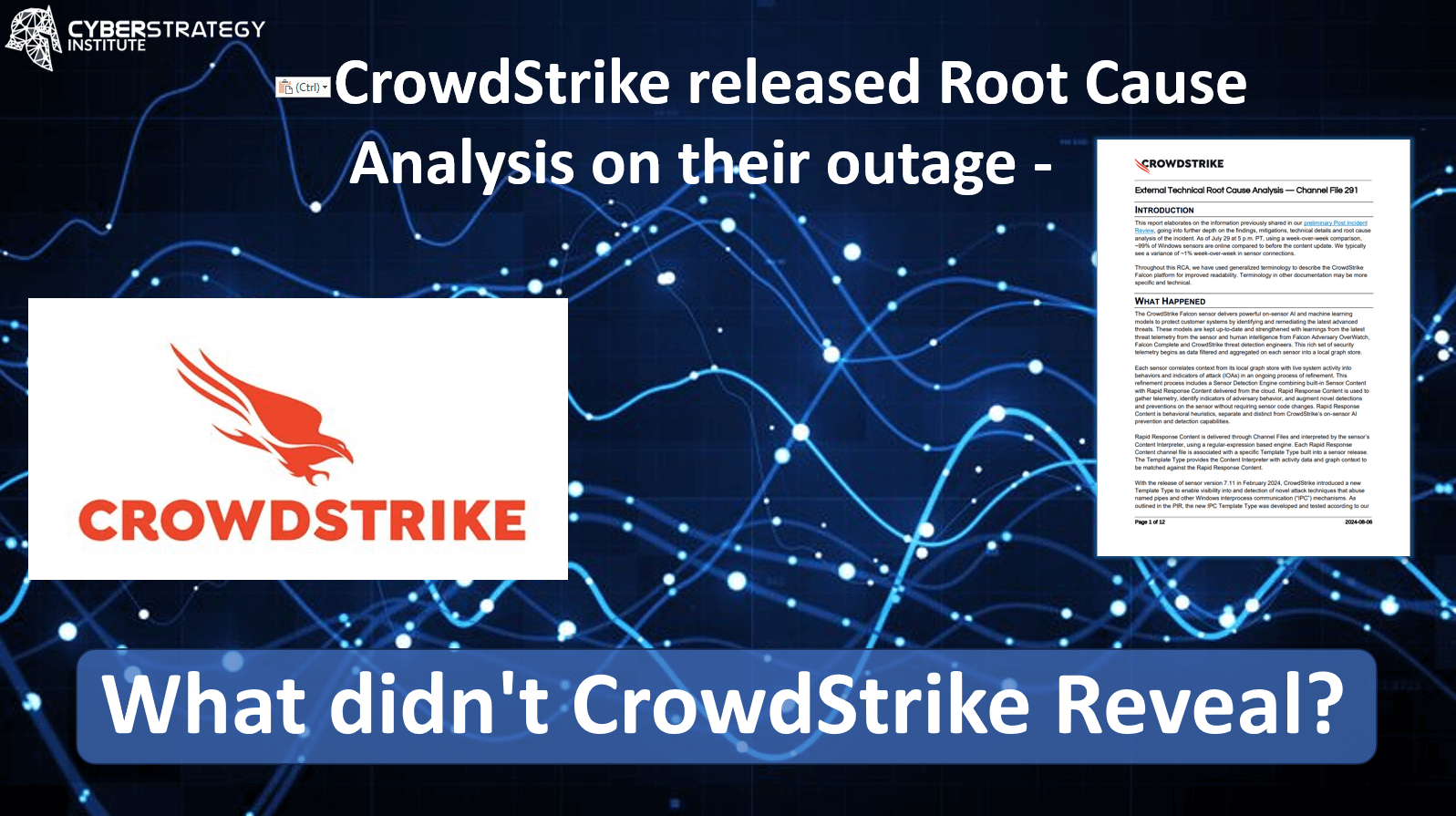
What didn’t CrowdStrike Reveal in their Incident Root Cause Analysis on the Outage?
CrowdStrike released Root Cause Analysis on the outage – What didn’t CrowdStrike Reveal? Overview In the rapidly evolving landscape of cybersecurity, even […]

What did Microsoft just admit about AI & AI Security out-loud? Breaking Down the Detection Flaws of the Microsoft Generative AI: The Case for Zero Trust
The Shortcomings of the Microsoft Detection-Based Cybersecurity Approach – How AI Security is Exposing the Fallacy of Detection Solutions. In an era […]

CrowdStrike Compromised: Unveiling the Hidden Threats in the Falcon CrowdStrike Outage Wake for CISOs
Architectural Flaws in CrowdStrike Caused the Outage in the CrowdStrike Update: Legal Protection for CISOs is More in Doubt Than Ever Before […]

Why Warden Zero Trust “Out-of-the-Box” Endpoint Defense Does Not Have the Same Problem as CrowdStrike Falcon
Revolutionizing Endpoint Protection: Warden Zero Trust “Out-of-the-Box” Containment vs. CrowdStrike’s Detection First Approach That Requires Frequent Kernel Updates In today’s cybersecurity landscape, […]

How Did the CrowdStrike Kernel Level Failure Impact 8.5M Microsoft Window Devices and Cause an IT Outage? – The Risks Cybersecurity Vendors Place their Clients Operations In
Crowdstrike Kernel Level Failure Just Impacted Everyday Life – 8M+ Systems in Air Travel, Banks, Emergency Services, Hospitals, and Backdoors Exploded in […]

Chinese Nation-State Hackers Breached Chemical Sector: Congressionally Discontinued CISA Program Linked to Ivanti Vulnerabilities Leading to a Breach, Affecting $639B Revenue, 3,200 Companies and 100,000 Individuals
CISA Warns of Hackers Breaching Ivanti Vulnerable Systems offline due to exploit impacting Chemical Security Tool, Exposing Sensitive Data The CISA Ivanti […]
What is the future of Security Operations Centers look like in 2024?
Exploring the Future of Security Operations Centers (SOCs) in 2024 What is a Security Operations Center (SOC)? With the rapid advancements in […]
