2024’s Cybersecurity Battle: Mitigating BianLian Ransomware Group Threats
Understanding BianLian Ransomware New Tactics and Indicators of Compromise Based on the vulnerabilities and risks described, basic attack paths towards compromise and ransomware […]
The Hidden Dangers: The Rise of Bespoke Malware and Ephemeral Infections
In-depth Analysis: Bespoke Malware and Ephemeral Infections What Are Bespoke Malware and Ephemeral Infections? Bespoke malware refers to custom-developed malicious software tailored […]
Understanding CPS: How Cyber-Physical Systems Connect the Digital and Cyber Physical System Worlds
2024 Cyber-Physical Systems (CPS) Security: A Comprehensive Analysis and Future Outlook In our technologically advanced era, Cyber-Physical Systems (CPS)—engineered to bridge digital […]
Why are Telemetry Pipelines Are Essential for Modern Data Management and Security?
Optimizing Telemetry Pipelines for Advanced Observability and Security: A Strategic Look into Warden’s Role and Competitive Landscape Telemetry pipelines are essential for […]
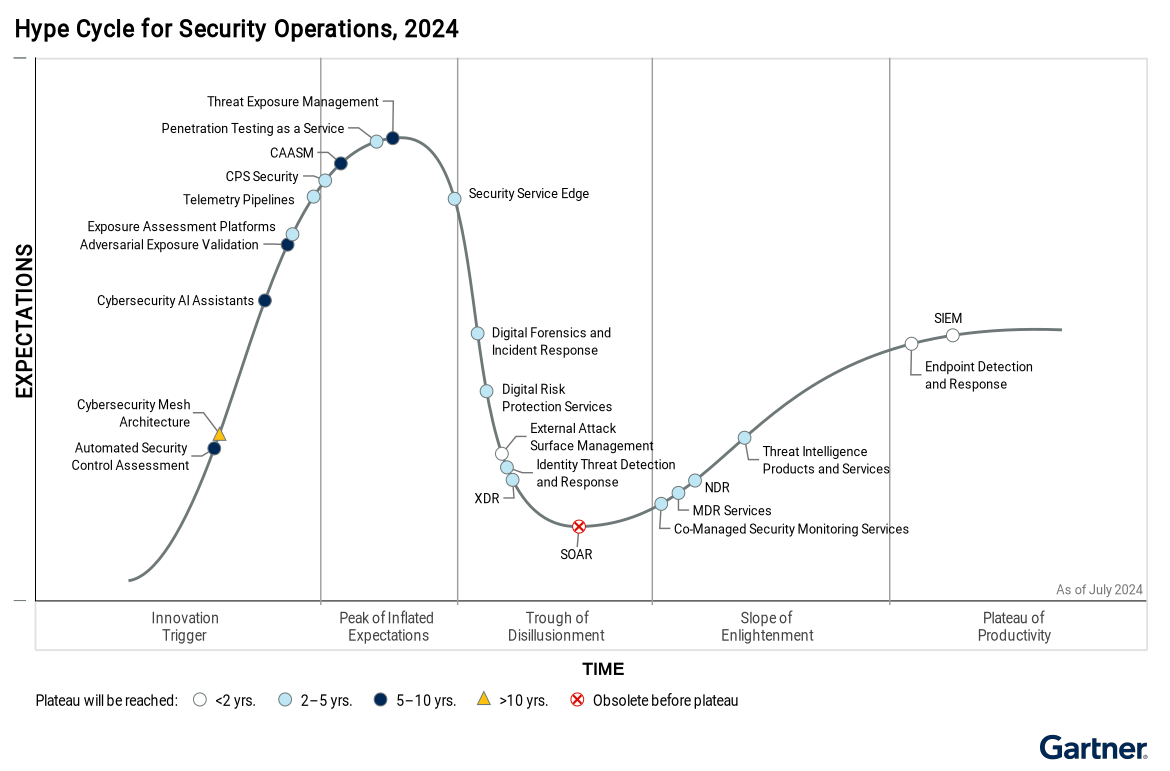
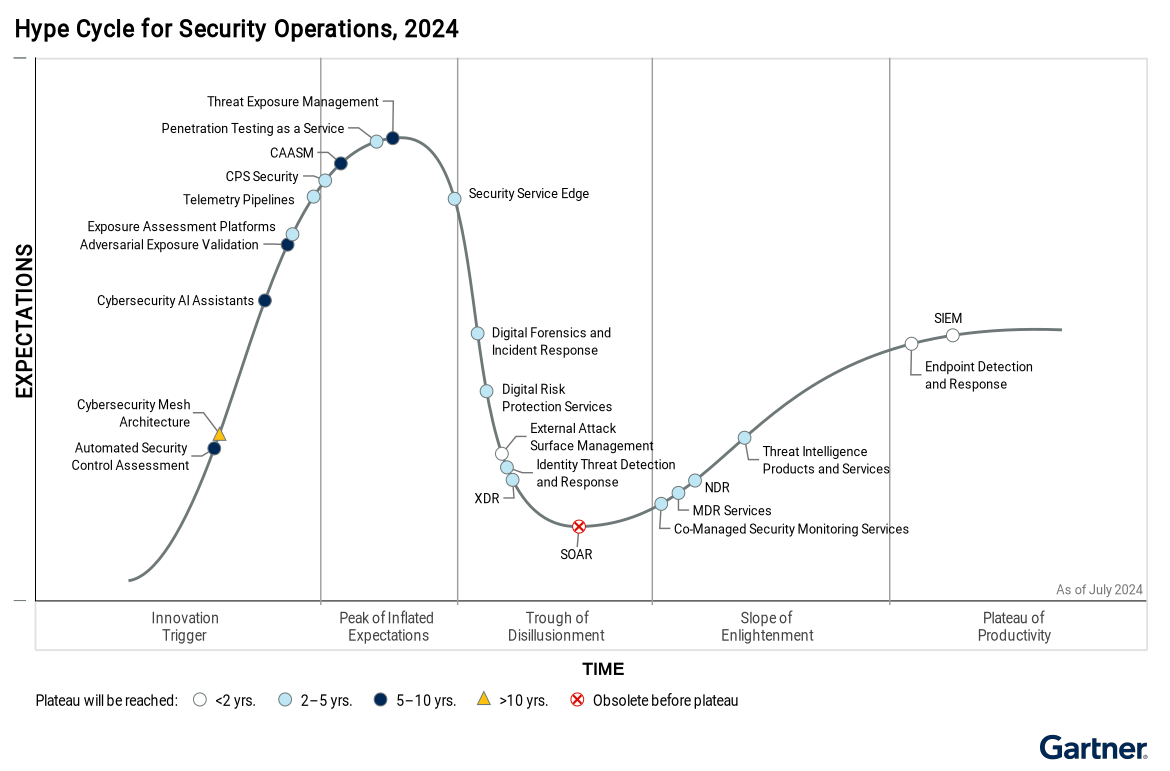
The Role of Adversarial Exposure Validation in 2024: A Key to CTEM Automation
Summary of Role of Adversarial Exposure Validation in CTEM from the 2024 Gartner Hype Cycle: Adversarial exposure validation (AEV) refers to technologies […]

Global Ransomware Attacks Strike in 52 Seconds: Why Prevention Beats Detection Every Time in this Crisis
Gone in 52 Seconds… The Global Ransomware Crisis and the Case for Warden In 2021 alone, 623.3 million ransomware attempts targeted organizations […]
Gartner Analysis of AI-Powered Cybersecurity Assistants: Will Generative AI Assistants Revolutionize Cybersecurity?
The Role of Cybersecurity AI Assistants: An In-Depth Analysis of Gartner’s 2024 Hype Cycle Cybersecurity AI assistants are on the brink of […]
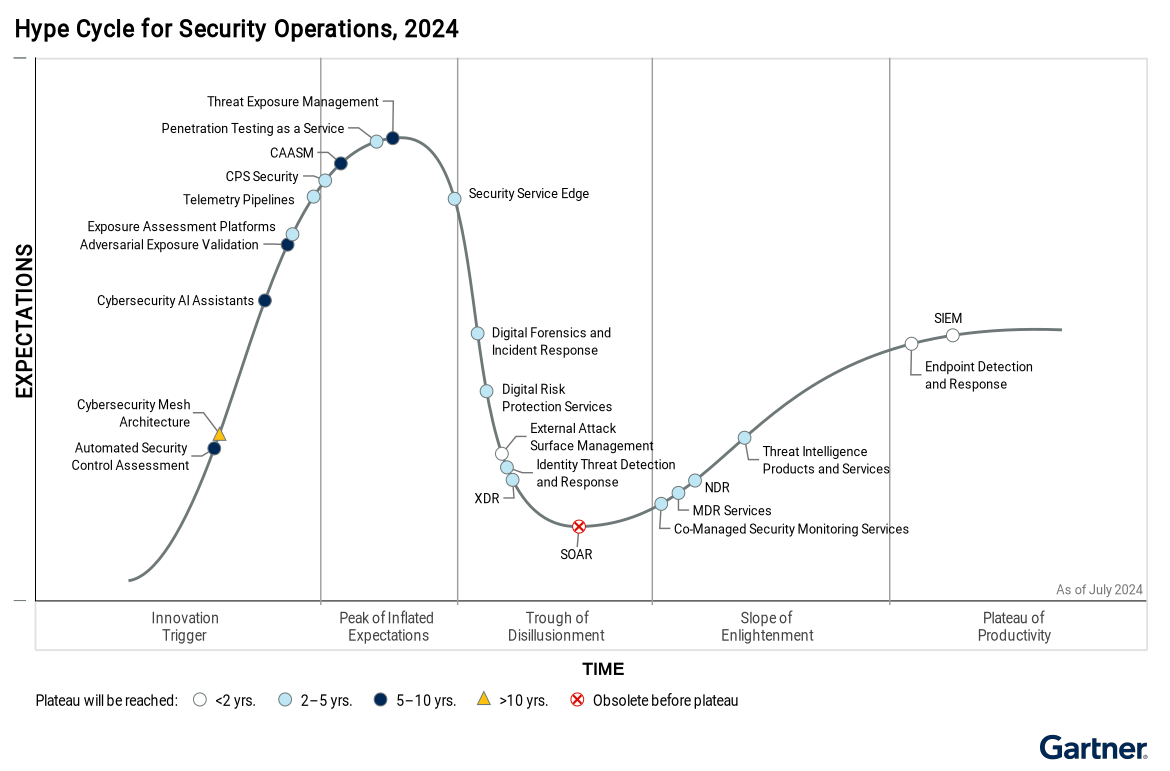
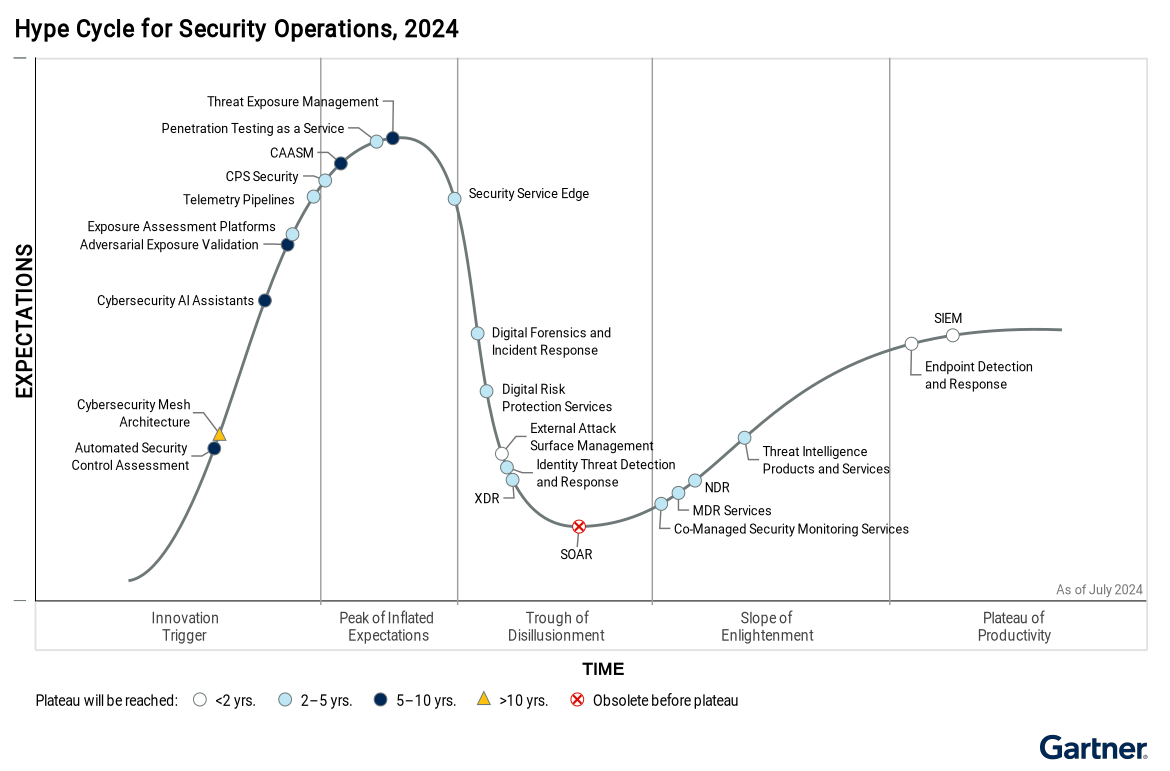
Gartner Analysis of Security Operations Centers (SOCs) in 2024 – Understanding the Hype Cycle™ for Security Operations
The Evolution of Cybersecurity Gartner Analysis of Security Operations Centers (SOCs) in 2024: New Trends, Challenges, and Innovations Gartner Analysis of Security Operations Centers […]
Microsoft States Zero Trust is the Future – Microsoft’s Endorsement is a Game Changer
Microsoft Endorsement for a Zero Trust Strategy As the digital landscape evolves, traditional security models are proving increasingly ineffective at preventing today’s […]
Navigating Zero Trust Security Solutions and Their Boundaries: Tough Questions Every Enterprise Should Ask in order to Implement Zero Trust
Key Considerations for Selecting and Avoiding Common Pitfalls in Implementing Zero Trust Security Solutions In today’s rapidly evolving cybersecurity landscape, Zero Trust […]

CISA has stated that K-12 Cybersecurity Threats are Rising – Schools have a way to onboard top Cybersecurity Solutions if they do…
Ransomware Attacks on Schools Are Escalating: How Schools Can Secure FCC Grants with a Proactive Cybersecurity Strategy Ransomware attacks on schools and […]

Why is Microsoft Allowing Hacks and the Case for Zero Trust?
Overview of Systemic Flaws Including Microsoft Security Failures and High-Profile Email Hacks Incident Summary In recent years, multiple high-profile cyberattacks have revealed […]
