Gartner Analysis of AI-Powered Cybersecurity Assistants: Will Generative AI Assistants Revolutionize Cybersecurity?
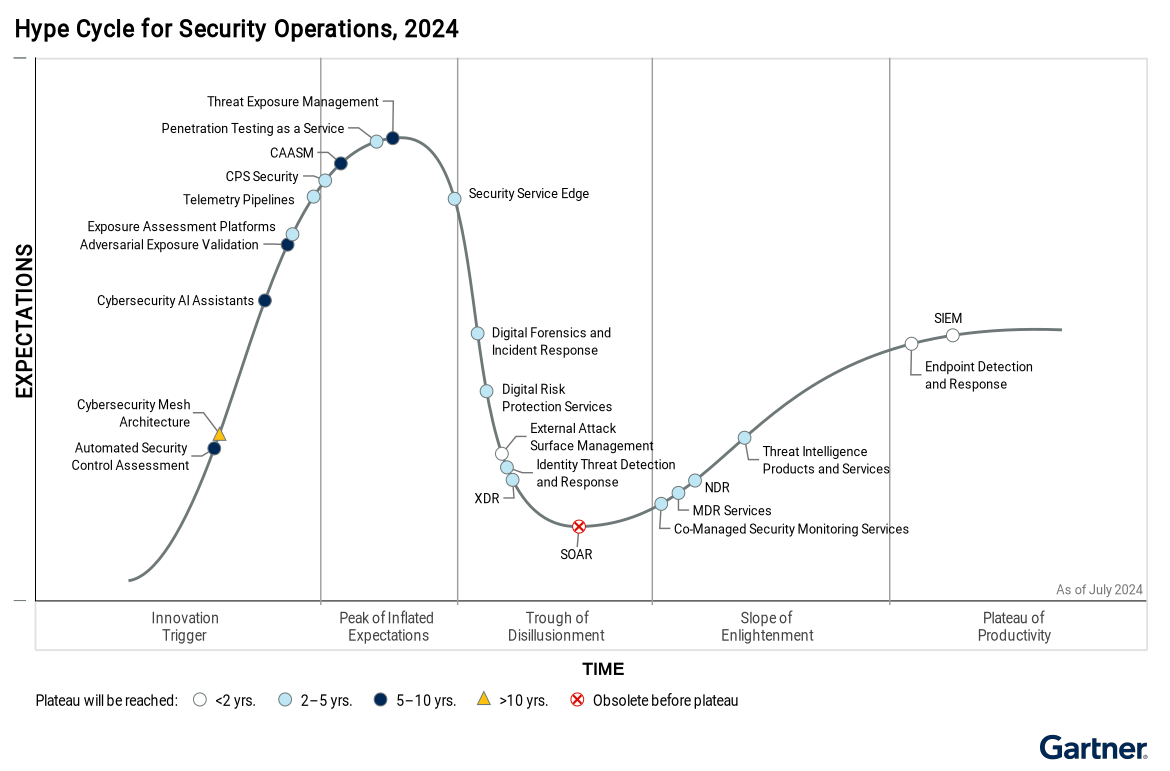
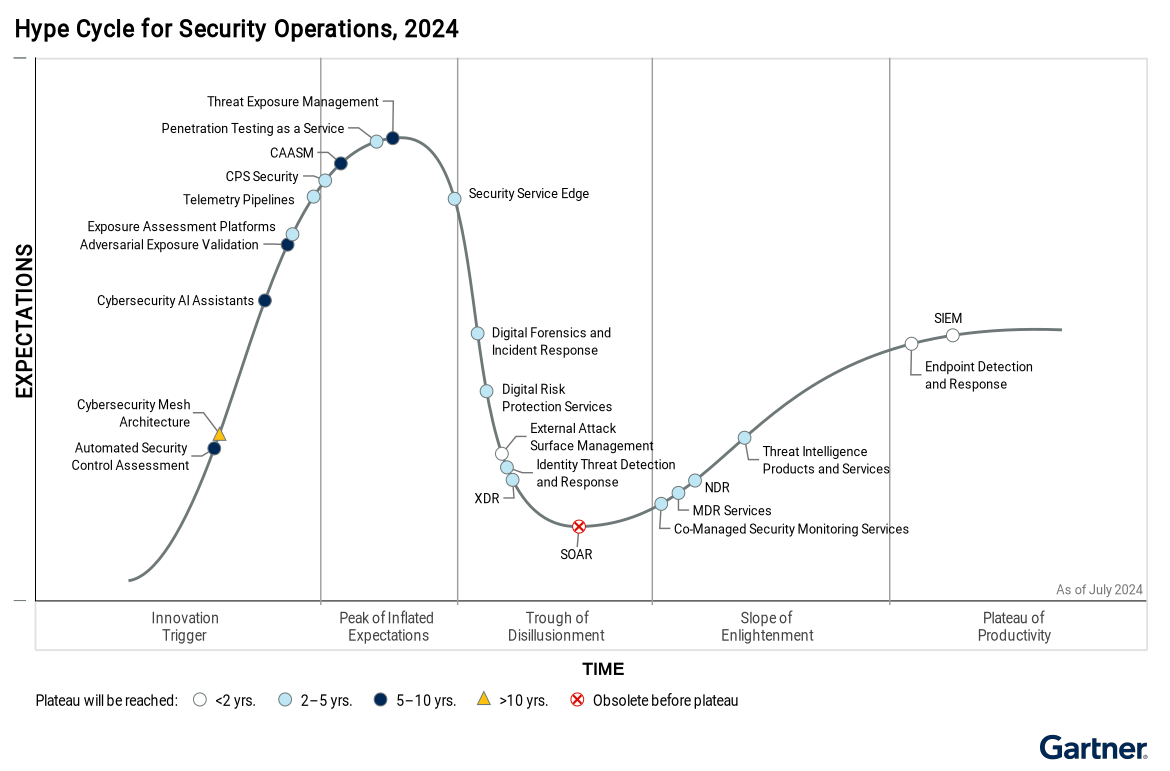
The Role of Cybersecurity AI Assistants: An In-Depth Analysis of Gartner’s 2024 Hype Cycle Cybersecurity AI assistants are on the brink of […]
Why Automated Security Control Assessment (ASCA) Is the Key to Unlocking Your Cyber Resilience in 2024
The Future of Automated Security Control Assessment (ASCA): Filling the Gaps in Gartner’s Hype Cycle In 2024, Gartner highlighted Automated Security Control […]
Cybersecurity in Healthcare Merger and Acquisition (M&A): Managing Risks to Ensure Successful M&A Integration and ROI
The Critical Importance of Due Diligence in Healthcare M&A: Safeguarding IT Assets and Mitigating Cybersecurity Risks As healthcare systems increasingly pursue mergers […]
Gartner Analysis of Security Operations Centers (SOCs) in 2024 – Understanding the Hype Cycle™ for Security Operations
The Evolution of Cybersecurity Gartner Analysis of Security Operations Centers (SOCs) in 2024: New Trends, Challenges, and Innovations Gartner Analysis of Security Operations Centers […]
Microsoft States Zero Trust is the Future – Microsoft’s Endorsement is a Game Changer
Microsoft Endorsement for a Zero Trust Strategy As the digital landscape evolves, traditional security models are proving increasingly ineffective at preventing today’s […]

How to Calculate the Cost of Downtime from IT to Cybersecurity Breach: A Complete Guide for 2024 on the True Cost of Downtime
The True Cost of Downtime and Data Breaches in 2024: What Small Businesses Need to Know In today’s fast-paced digital world, nothing […]
Ethical Dilemmas in Pentagon Cyberdefense a Case Study: Why Did HP Enterprise Let Russia Scrutinize ArcSight?
HP Enterprise Allowed a Russian Defense Agency to Review ArcSight Cybersecurity Software Used by the Pentagon – Why? Why did Hewlett Packard […]
Advanced Pentesting with Horizon3.ai: How NodeZero Tripwires™ Neutralize Attack Vectors
The Cyber Battle You Can’t Afford to Lose: How Pentesting and NodeZero Tripwires™ Can Save Your Network In today’s digital landscape, your […]
Navigating Zero Trust Security Solutions and Their Boundaries: Tough Questions Every Enterprise Should Ask in order to Implement Zero Trust
Key Considerations for Selecting and Avoiding Common Pitfalls in Implementing Zero Trust Security Solutions In today’s rapidly evolving cybersecurity landscape, Zero Trust […]

CISA has stated that K-12 Cybersecurity Threats are Rising – Schools have a way to onboard top Cybersecurity Solutions if they do…
Ransomware Attacks on Schools Are Escalating: How Schools Can Secure FCC Grants with a Proactive Cybersecurity Strategy Ransomware attacks on schools and […]

Why is Microsoft Allowing Hacks and the Case for Zero Trust?
Overview of Systemic Flaws Including Microsoft Security Failures and High-Profile Email Hacks Incident Summary In recent years, multiple high-profile cyberattacks have revealed […]

How to Secure State and Local Cybersecurity Grants: A Step-by-Step Guide for those Wanting FCC School and Library Grant Funding
Introduction for Those Looking for State and Local Cybersecurity Grant Programs for K-12 Schools With the increasing frequency of cybersecurity threats in […]
