The Role of Adversarial Exposure Validation in 2024: A Key to CTEM Automation
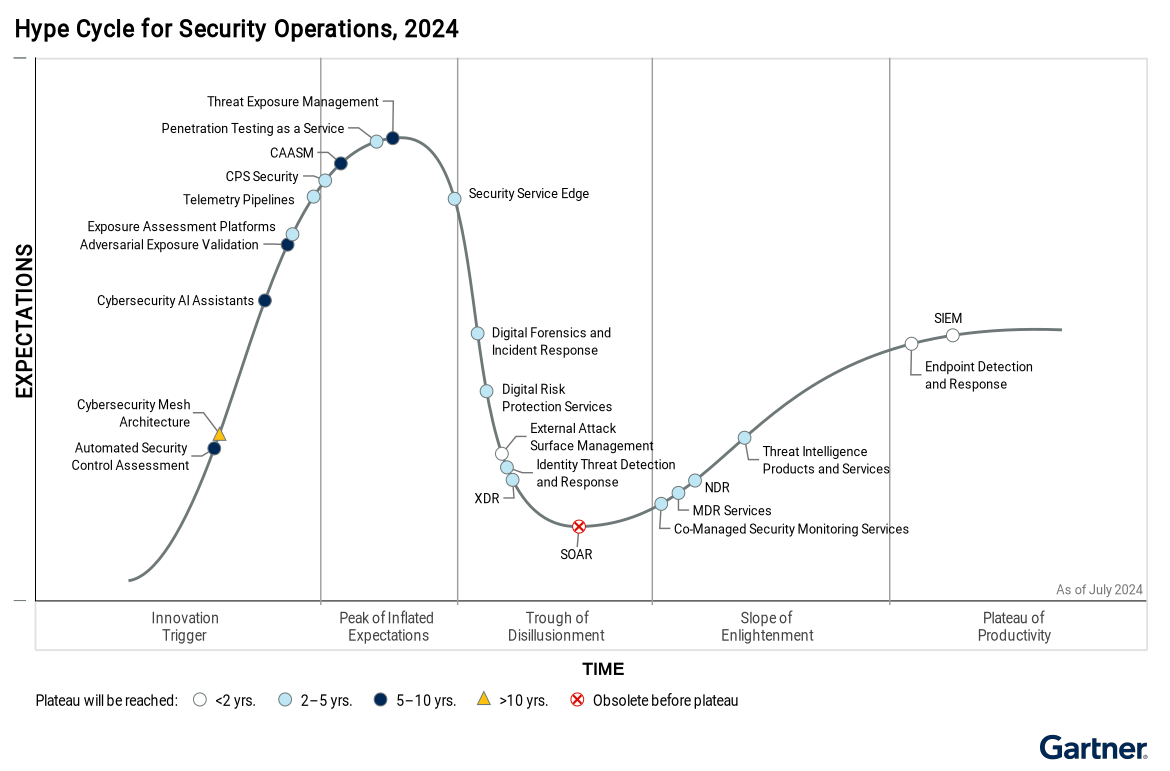
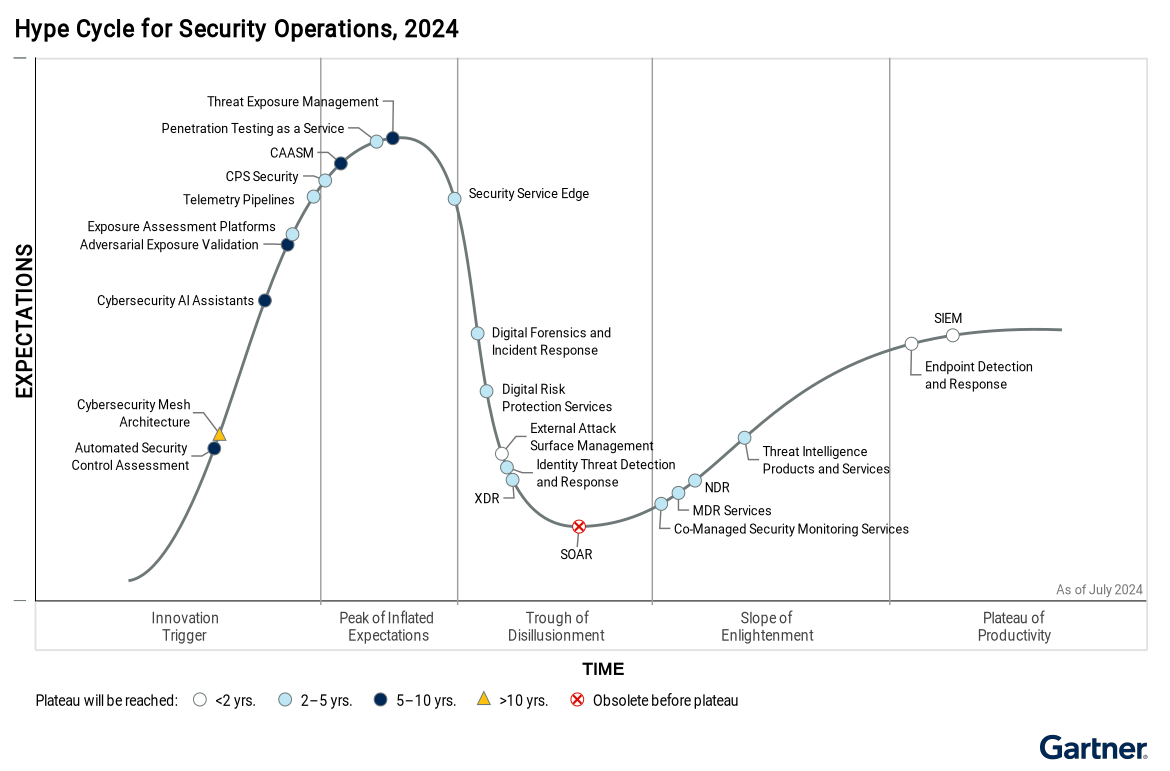
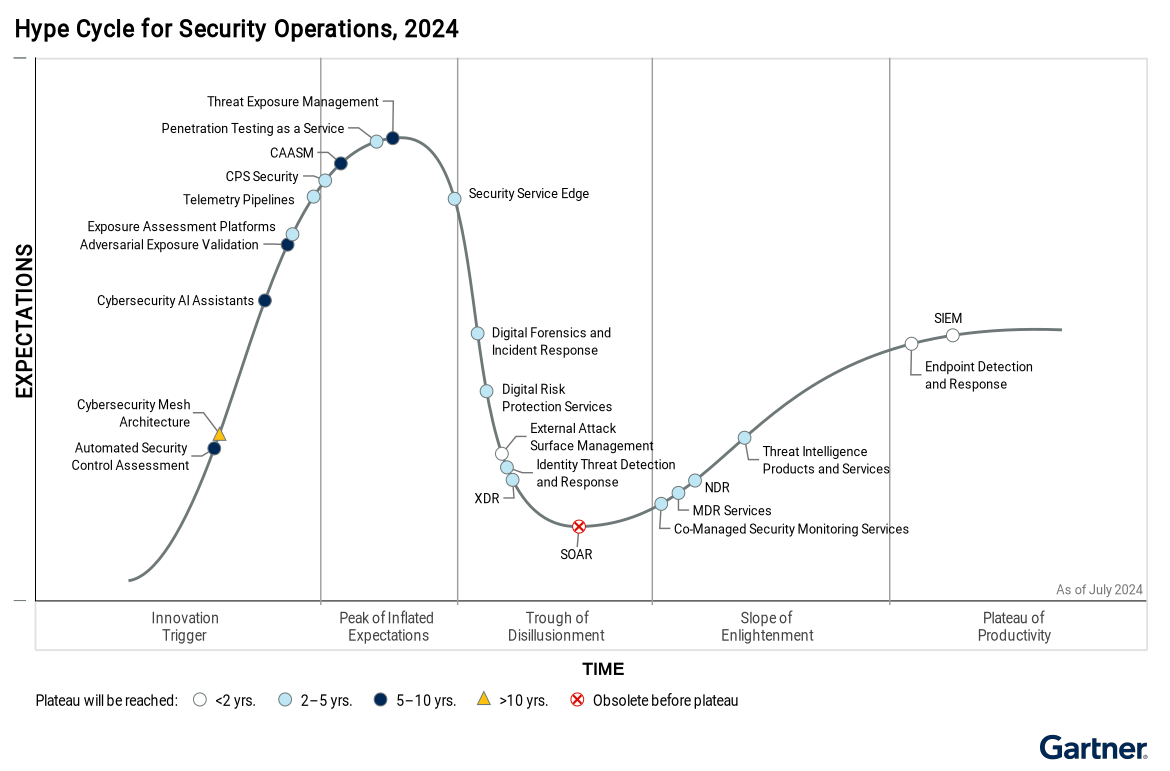
Summary of Role of Adversarial Exposure Validation in CTEM from the 2024 Gartner Hype Cycle: Adversarial exposure validation (AEV) refers to technologies […]
Gartner Analysis of AI-Powered Cybersecurity Assistants: Will Generative AI Assistants Revolutionize Cybersecurity?
The Role of Cybersecurity AI Assistants: An In-Depth Analysis of Gartner’s 2024 Hype Cycle Cybersecurity AI assistants are on the brink of […]
Why Automated Security Control Assessment (ASCA) Is the Key to Unlocking Your Cyber Resilience in 2024
The Future of Automated Security Control Assessment (ASCA): Filling the Gaps in Gartner’s Hype Cycle In 2024, Gartner highlighted Automated Security Control […]
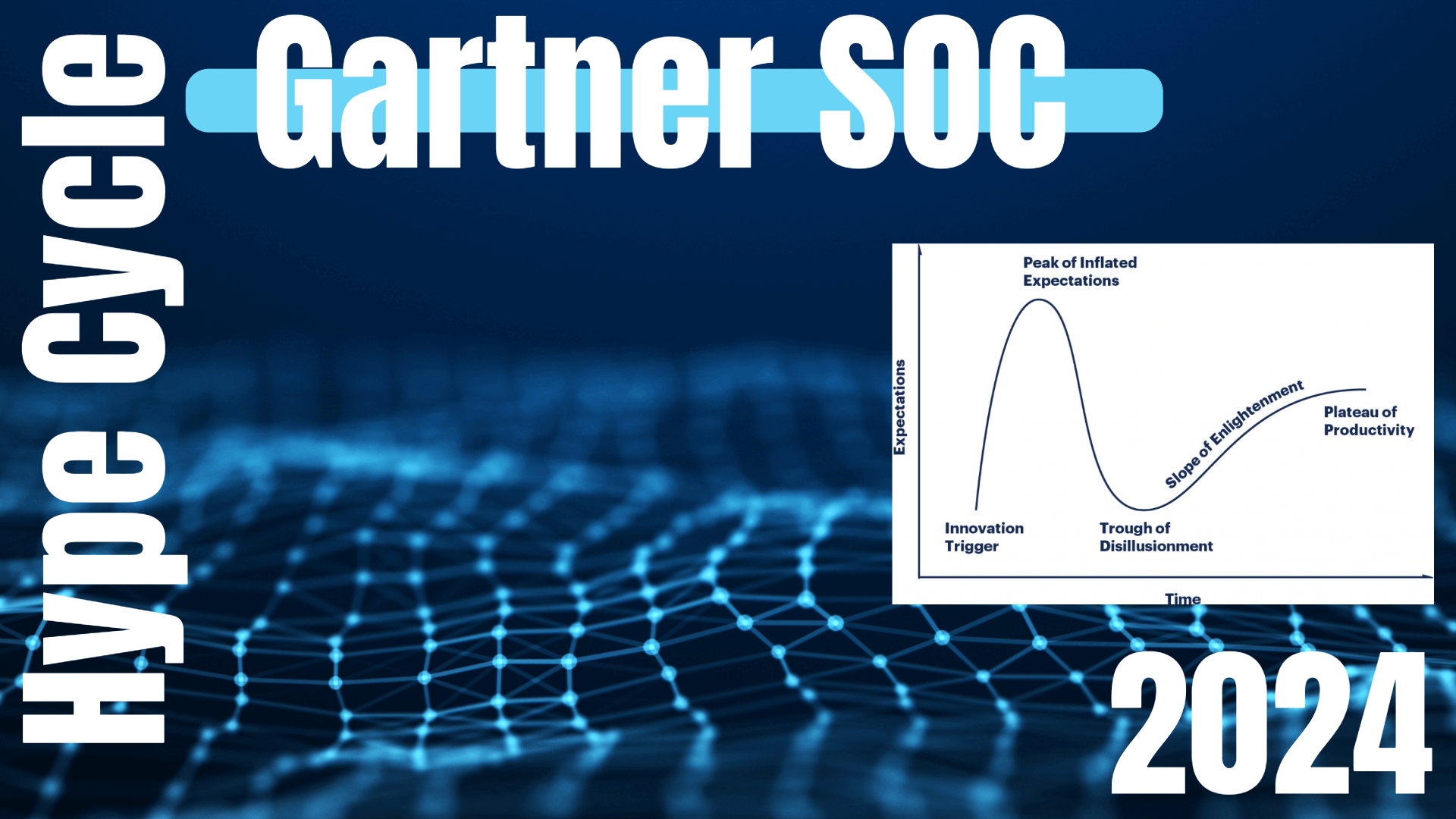
Gartner Analysis of Security Operations Centers (SOCs) in 2024 – Understanding the Hype Cycle™ for Security Operations
The Evolution of Cybersecurity Gartner Analysis of Security Operations Centers (SOCs) in 2024: New Trends, Challenges, and Innovations Gartner Analysis of Security Operations Centers […]

How to Secure State and Local Cybersecurity Grants: A Step-by-Step Guide for those Wanting FCC School and Library Grant Funding
Introduction for Those Looking for State and Local Cybersecurity Grant Programs for K-12 Schools With the increasing frequency of cybersecurity threats in […]
Sinkclose Vulnerability in Hundreds of Millions of AMD Chips Allows Unfixable Flaw & Possible Infections to Bootkits – Learn What to do Now!
Sinkclose Vulnerability Explained: How to Secure Your AMD Chips Flaws AMD Chip Flaw Overview of Sinkclose Security flaws within firmware, the core […]

Chinese Nation-State Hackers Breached Chemical Sector: Congressionally Discontinued CISA Program Linked to Ivanti Vulnerabilities Leading to a Breach, Affecting $639B Revenue, 3,200 Companies and 100,000 Individuals
CISA Warns of Hackers Breaching Ivanti Vulnerable Systems offline due to exploit impacting Chemical Security Tool, Exposing Sensitive Data The CISA Ivanti […]
The Illusion of Safety: Why VPNs Aren’t Foolproof as a result of the “TunnelVision” Security Vulnerability!
The Flawed Foundation— Facing the Limitations of VPN Security now that Every VPN is at Risk! A critical security vulnerability called “TunnelVision” that […]
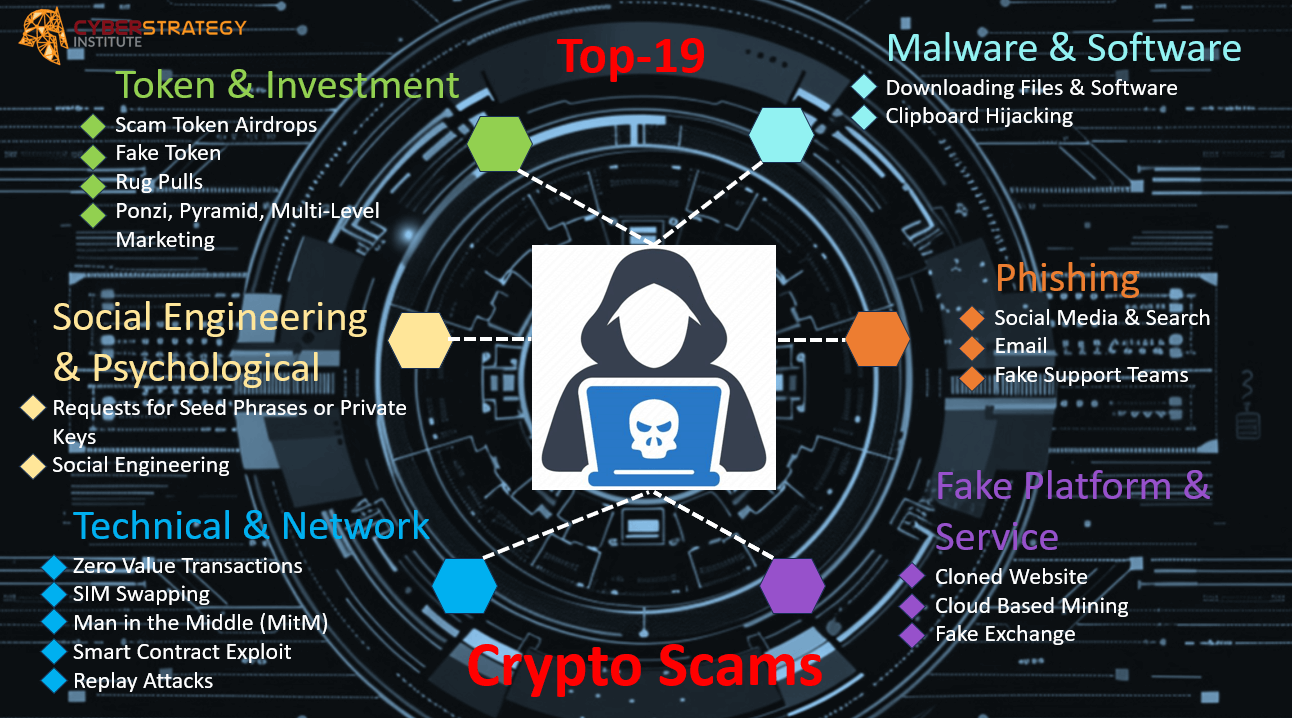
Pixel Fortresses: The Vanguard of Web3 Gaming Security
Building unbreakable bonds between pixels and protection in the era of digital ownership. Introduction: A New Epoch of Entertainment The digital realm […]

AI Security — Top 5 Things You Need to Know
In the dynamic landscape of Artificial Intelligence (AI), ensuring robust security measures is paramount as AI becomes our new crown-jewel. The evolving […]
Unraveling Cybersecurity: A Critical Reassessment of Traditional Solutions to Protect Your Company
Unraveling Cybersecurity: Rethinking Traditional Solutions to Protect Your Business Cybersecurity strategies for business continuity are crucial for businesses in today’s landscape, with […]